
Hackers are exploiting a essential ownCloud vulnerability tracked as CVE-2023-49103 that exposes admin passwords, mail server credentials, and license keys in containerized deployments.
ownCloud is a broadly used open-source file synchronization and sharing answer designed for individuals who want to handle and share knowledge by a self-hosted platform.
On November 21, the software program’s builders printed safety bulletins for 3 vulnerabilities that would result in knowledge breaches, urging ownCloud directors to use the advisable mitigations instantly.
Of the three flaws, CVE-2023-49103 obtained a most CVSS severity rating of 10.0 because it permits a distant risk actor to execute phpinfo() by the ownCloud ‘graphapi’ app, which reveals the server’s atmosphere variables, together with credentials saved inside them.
“In containerized deployments, these atmosphere variables could embody delicate knowledge such because the ownCloud admin password, mail server credentials, and license key,” reads the CVE-2023-49103 advisory.
Additionally, if different companies in the identical atmosphere use the identical variants and configurations, the identical credentials can be utilized to entry these companies as nicely, increasing the breach.
Energetic exploitation underway
Sadly, leveraging CVE-2023-49103 for knowledge theft assaults is not sophisticated, and risk actors have already been found exploiting the flaw in assaults.
Risk monitoring agency Greynoise reported yesterday that it noticed mass exploitation of the flaw within the wild beginning on November 25, 2023, with a rising trajectory. Greynoise tracked 12 distinctive IP addresses exploiting CVE-2023-49103.
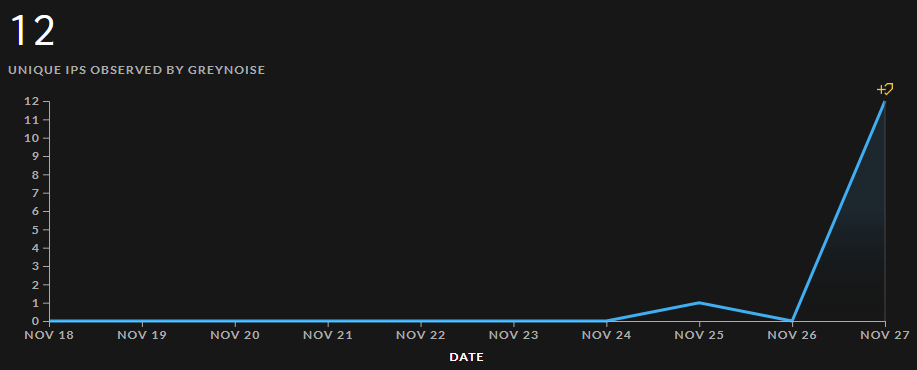
Supply: Greynoise
Shadowserver additionally studies related observations, warning that it at the moment detects over 11,000 susceptible cases, with most situated in Germany, america, France, and Russia.
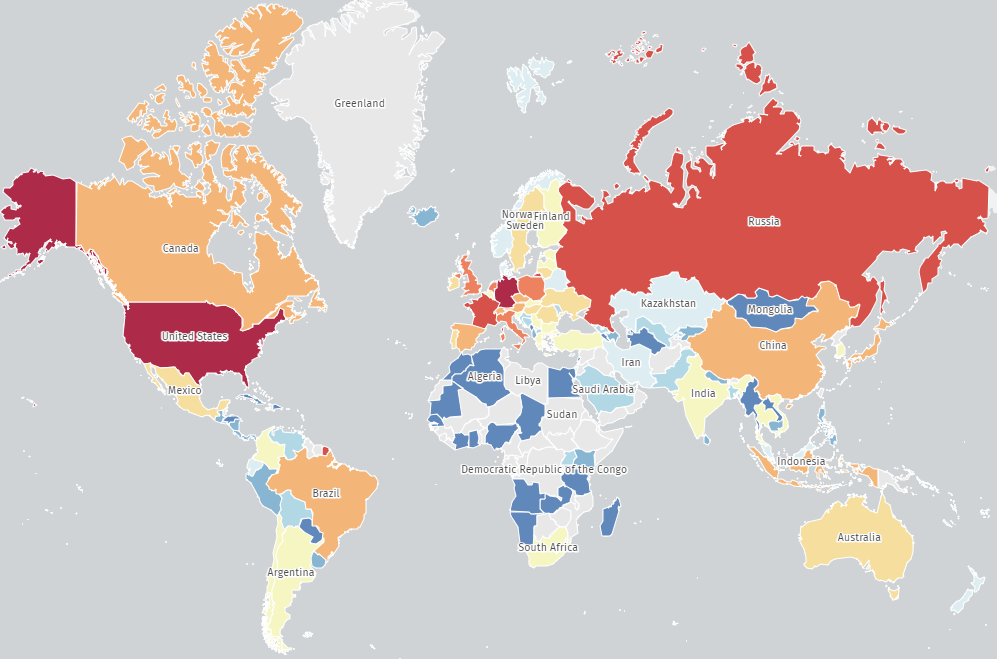
Supply: Shadowserver
As a result of elevated exploitation of this flaw, ownCloud directors are advisable to take rapid motion to remediate the danger.
The advisable repair is to delete the ‘owncloud/apps/graphapi/vendor/microsoft/microsoft-graph/assessments/GetPhpInfo.php’ file, disable the ‘phpinfo’ operate in Docker containers, and alter probably uncovered secrets and techniques just like the ownCloud admin password, mail server, database credentials, and Object-Retailer/S3 entry keys.
It is very important observe that disabling the graphapi app doesn’t mitigate the risk, which is equally extreme for each containerized and non-containerized environments.
The one case immune to the credential disclosure downside is Docker containers created earlier than February 2023.


