
The Lumma information-stealer malware (aka ‘LummaC2’) is selling a brand new function that allegedly permits cybercriminals to revive expired Google cookies, which can be utilized to hijack Google accounts.
Session cookies are particular internet cookies used to permit a searching session to log in to an internet site’s companies robotically. As these cookies enable anybody possessing them to log in to the proprietor’s account, they generally have a restricted lifespan for safety causes to forestall misuse if stolen.
Restoring these cookies would enable Lumma operators to realize unauthorized entry to any Google account even after the respectable proprietor has logged out of their account or their session has expired.
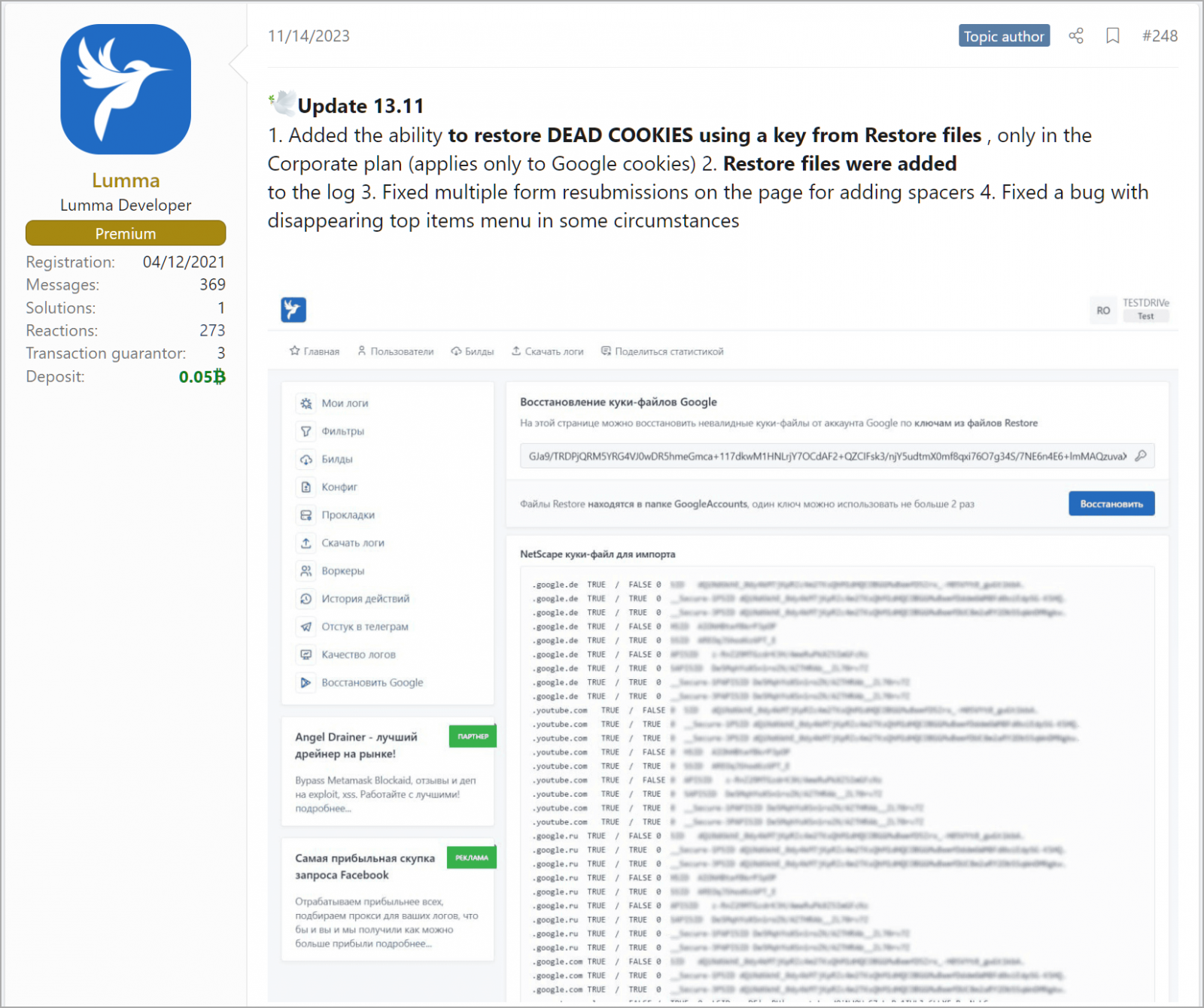
Hudson Rock’s Alon Gal first noticed a discussion board submit by the info-stealer’s builders highlighting an replace launched on November 14, claiming the “potential to revive useless cookies utilizing a key from restore information (applies solely to Google cookies).”
Supply: BleepingComputer
This new function was solely made obtainable to subscribers of the highest-tier “Company” plan, which prices cybercriminals $1,000/month.
The discussion board submit additionally clarifies that every key can be utilized twice in order that cookie restoration can work just one time. That will nonetheless be sufficient to launch catastrophic assaults on organizations that in any other case comply with good safety practices.
This new function allegedly launched in current Lumma releases is but to be verified by safety researchers or Google, so whether or not or not it really works as marketed stays unsure.
Nevertheless, it’s value mentioning that one other stealer, Rhadamanthys, introduced the same functionality in a current replace, rising the chance that malware authors found an exploitable safety hole.
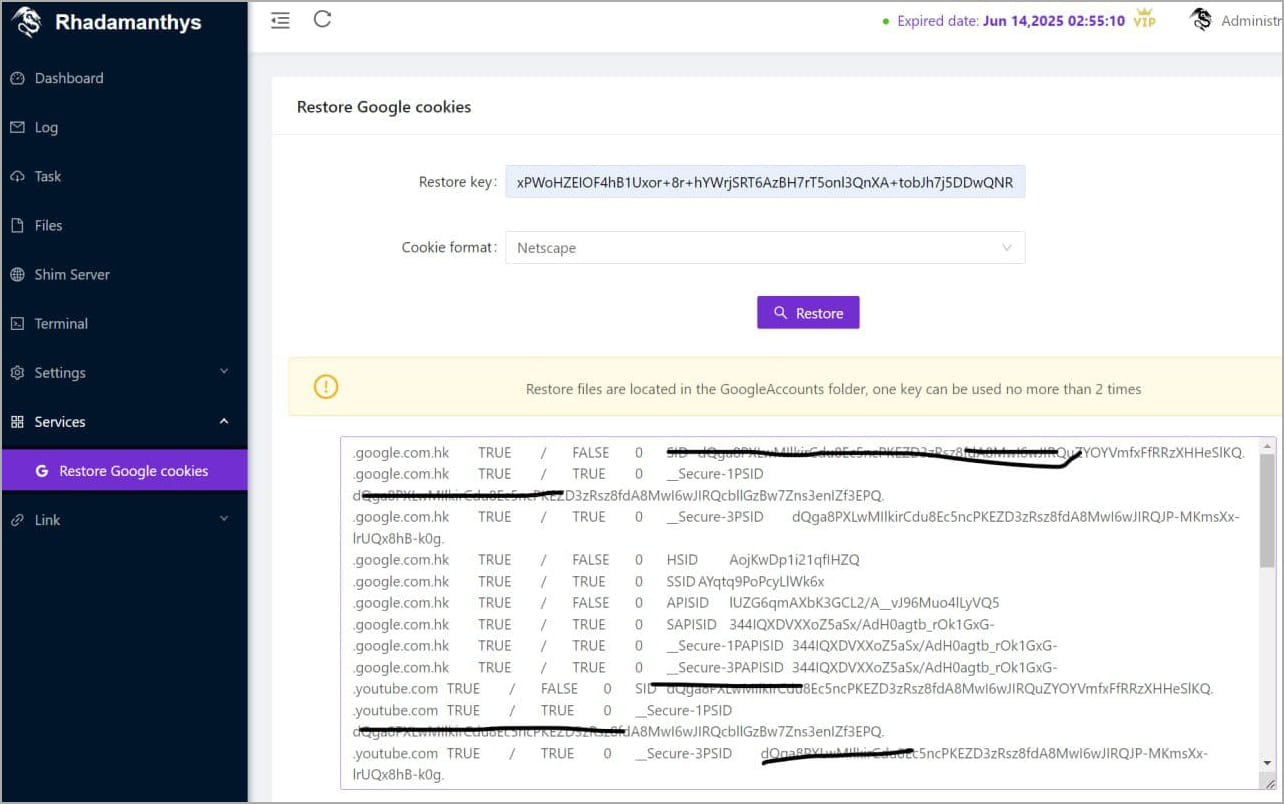
Supply: @g0njxa
BleepingComputer has contacted Google a number of instances requesting a touch upon the potential of malware authors having found a vulnerability in session cookies, however we’ve got but to obtain a response.
Just a few days after contacting Google, Lumma’s builders launched an replace that claims to be an extra repair to bypass newly launched restrictions imposed by Google to forestall cookie restoration.
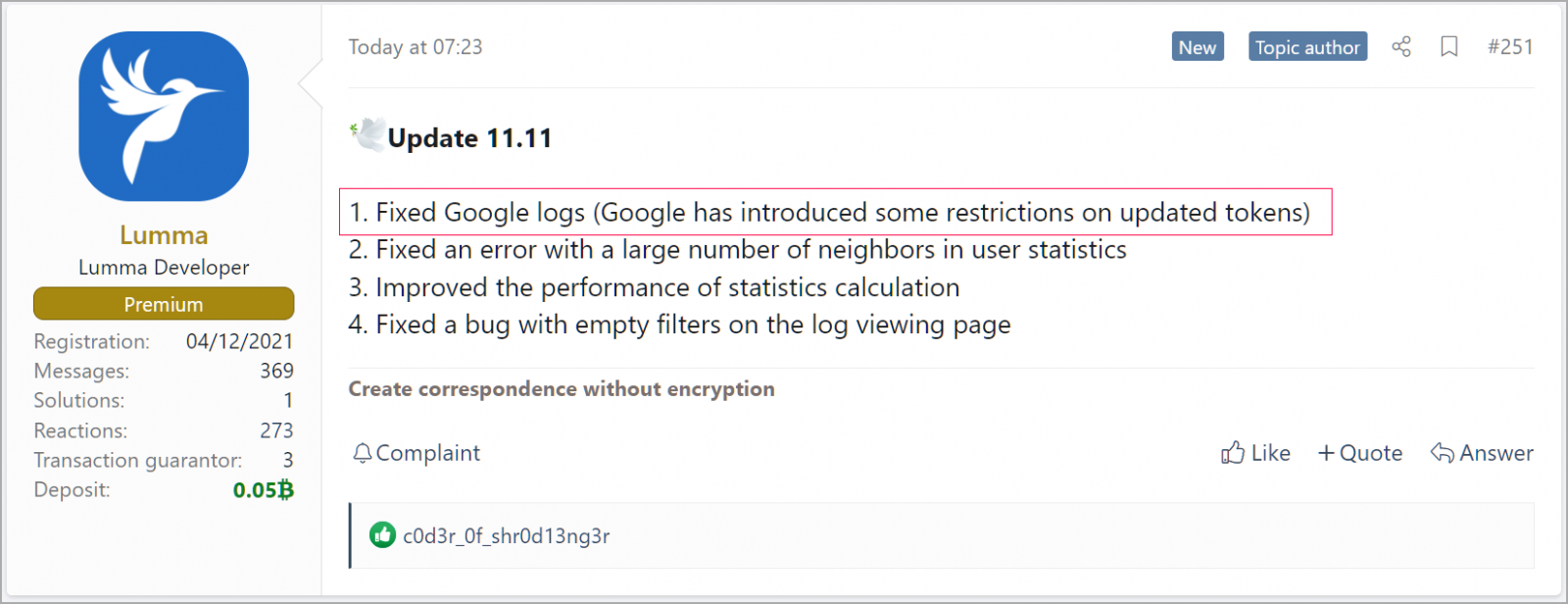
Supply: BleepingComputer
BleepingComputer has additionally tried to be taught extra about how the function works and what weak spot it exploits instantly from Lumma. Nevertheless, a “assist agent” of the malware operation declined to share something about it.
When requested about the same function Rhadamantis added just lately, Lumma’s agent advised us their opponents had carelessly copied the function from their stealer.
If information-stealers can certainly restore expired Google cookies as promoted, there’s nothing that customers can do to guard their accounts till Google pushes out a repair in addition to stopping the malware an infection that results in the theft of these cookies.
Precautions embrace avoiding downloads of torrent information and executables from doubtful web sites and skipping promoted leads to Google Search.


