North Korean menace actors have been linked to 2 campaigns through which they masquerade as each job recruiters and seekers to distribute malware and procure unauthorized employment with organizations based mostly within the U.S. and different elements of the world.
The exercise clusters have been codenamed Contagious Interview and Wagemole, respectively, by Palo Alto Networks Unit 42.
Whereas the primary set of assaults goals to “infect software program builders with malware via a fictitious job interview,” the latter is designed for monetary achieve and espionage.
“The primary marketing campaign’s goal is probably going cryptocurrency theft and utilizing compromised targets as a staging atmosphere for added assaults,” the cybersecurity firm stated.
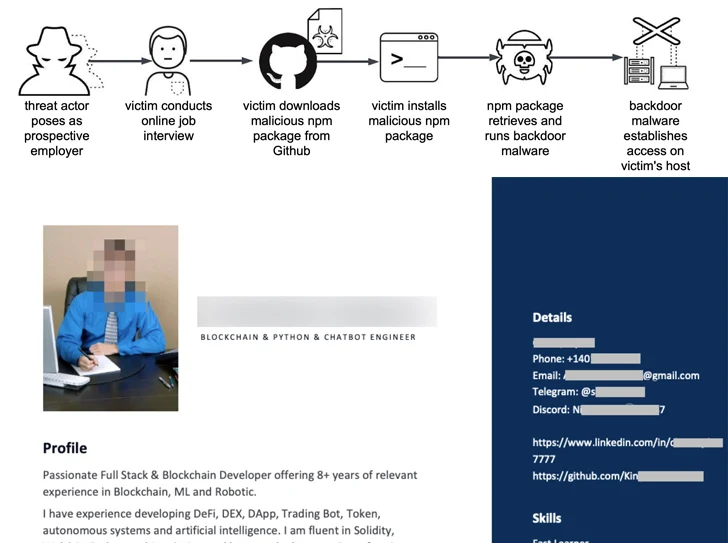
The fraudulent job-seeking exercise, alternatively, entails the usage of a GitHub repository to host resumes with solid identities that impersonate people of assorted nationalities.
The Contagious Interview assaults pave the best way for 2 hitherto undocumented cross-platform malware named BeaverTail and InvisibleFerret that may run on Home windows, Linux, and macOS methods.
It is value noting that the intrusion set shares tactical overlaps with beforehand reported North Korean menace exercise dubbed Operation Dream Job, which entails approaching workers with potential job provides and tricking them into downloading a malicious npm package deal hosted on GitHub as a part of a web based interview.
“The menace actor seemingly presents the package deal to the sufferer as software program to evaluate or analyze, but it surely really incorporates malicious JavaScript designed to contaminate the sufferer’s host with backdoor malware,” Unit 42 stated.
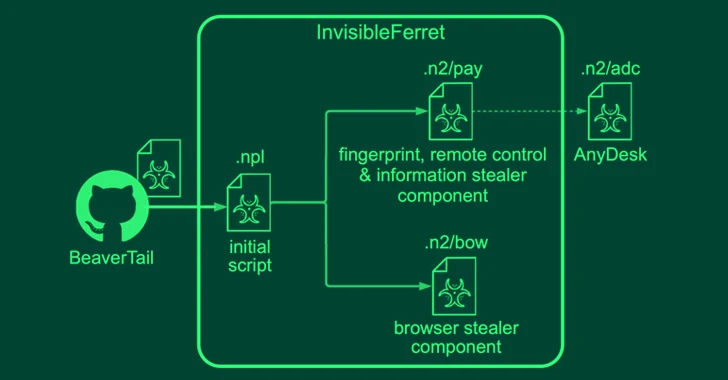
BeaverTail, the JavaScript implant, is a stealer and a loader that comes with capabilities to steal delicate data from internet browsers and crypto wallets, and ship further payloads, together with InvisibleFerret, a Python-based backdoor with fingerprinting, distant management, keylogging, and knowledge exfiltration options.
InvisibleFerret can also be designed to obtain the AnyDesk shopper from an actor-controlled server for distant entry.
Earlier this month, Microsoft warned that the notorious Lazarus Group sub-cluster known as Sapphire Sleet (aka BlueNoroff) has established new infrastructure that impersonates abilities evaluation portals as a part of its social engineering campaigns.
This isn’t the primary time North Korean menace actors have abused bogus modules in npm and PyPI. In late June and July 2023, Phylum and GitHub detailed a social engineering marketing campaign focusing on the private accounts of workers working in know-how corporations with the purpose of putting in a counterfeit npm package deal below the guise of collaborating on a GitHub venture.
The assaults have been attributed to a different cluster generally known as Jade Sleet, which can also be referred to as TraderTraitor and UNC4899, and has since been implicated within the JumpCloud hack that happened across the identical time.
The invention of Wagehole echoes a latest advisory from the U.S. authorities, which disclosed North Korea’s subterfuge to beat sanctions by dispatching a military of highly-skilled IT staff who acquire employment in a number of firms globally and funnel again their wages to fund the nation’s weapons packages.
“Some resumes embody hyperlinks to a LinkedIn profile and hyperlinks to GitHub content material,” the cybersecurity firm stated.
“These GitHub accounts seem properly maintained and have a prolonged exercise historical past. These accounts point out frequent code updates and socialization with different builders. In consequence, these GitHub accounts are practically indistinguishable from reputable accounts.”
“We might create 20 to 50 pretend profiles a 12 months till we had been employed,” a North Korean IT employee who just lately defected was quoted as saying to Reuters, which additionally shared particulars of the Wagemole marketing campaign.
The event comes as North Korea claimed that it has efficiently put a navy spy satellite tv for pc into area, after two unsuccessful makes an attempt in Could and August of this 12 months.
It additionally follows a new assault marketing campaign orchestrated by the North Korea-linked Andariel group – one other subordinate ingredient inside Lazarus – to ship Black RAT, Lilith RAT, NukeSped, and TigerRAT by infiltrating susceptible MS-SQL servers in addition to by way of provide chain assaults utilizing a South Korean asset administration software program.
“Software program builders are sometimes the weakest hyperlink for provide chain assaults, and fraudulent job provides are an ongoing concern, so we anticipate continued exercise from Contagious Interview,” Unit 42 stated. “Moreover, Wagemole represents a possibility to embed insiders in focused firms.”