As software program improvement focuses on steady integration and deployment, orchestration platforms like Kubernetes have taken off, however that recognition has put them in attackers’ crosshairs.
Most profitable assaults — not less than these publicly reported — have led to the deployment of cryptomining-focused containers, principally stealing cloud compute sources from companies to energy cryptocurrency mining. But the assaults could possibly be a lot worse — infecting Kubernetes clusters with rootkits would end in collections of containers managed by attackers, says Nicholas Lang, a safety researcher with cloud-infrastructure safety agency Sysdig, who will current a prototype rootkit at Black Hat Europe subsequent month.
The profitable compromise of a Kubernetes cluster by a rootkit may enable an attacker to cover malicious containers on the system, for instance. The rootkit can conceal different containerized payloads and take extra refined actions escaping discover within the system, as a result of they’re hidden from the working system, he says.
“Though it interacts with the kernel to get these containers up and in place, after that … the rootkit is ready to conceal these containerized payloads,” Lang says. “The rootkit is a part of the preliminary payload … after which, you understand, future phases will do extra refined issues in secret as a result of they’re hidden from the working system by the rootkit.”
Kubernetes is a well-liked method of automating the configuration, deployment, and administration — that’s, “orchestration” — of containers, virtualized software program environments that may run all kinds of workloads, from servers to functions to software-defined networks. As such, the expertise is essential for cloud functions in at present’s fast-moving world of software program improvement and deployment.
For a similar motive, nonetheless, attackers have focused the infrastructure. In February, an attacker compromised a misconfigured Kubernetes cluster, first putting in cryptojacking containers after which stealing mental property and delicate knowledge. A month earlier, Microsoft researchers found that the Kinsing malware had began focusing on poorly configured database containers on Kubernetes platforms.
Kubernetes Underneath Assault
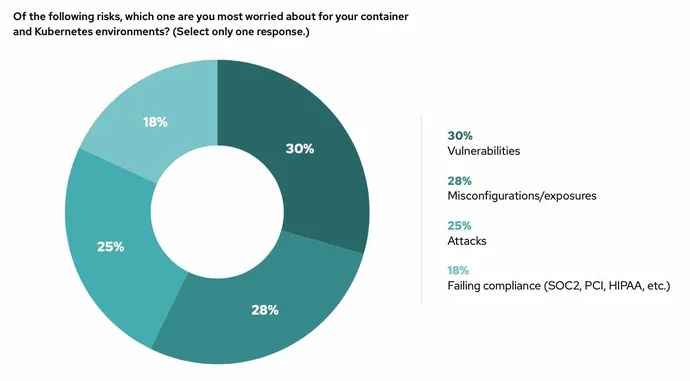
The spate of assaults have software program corporations fearful. Two-thirds of corporations (67%) have delayed or slowed down an utility deployment attributable to a safety concern with Kubernetes, in response to Crimson Hat’s “2023 State of Kubernetes Safety Report.”
Whereas attackers have exploited vulnerabilities in Kubernetes infrastructure, misconfigured functions working in containers are, by far, the most typical method that the orchestration platform is compromised, says Sysdig’s Lang.
“A misconfigured Internet server or Internet utility provides the attacker shell entry to that digital machine or inside that container,” he says. “Relying on the attacker’s sophistication degree, they’re going to both understand that they are inside a container or a digital machine, or no matter, and attempt to escape to the host, or they understand that they are in a Kubernetes setting by doing a bit of little bit of poking and prodding.”
Whereas a selected Linux kernel rootkit, referred to as Diamorphine, has sometimes been used to compromise Kubernetes clusters, Kubernetes-focused rootkits haven’t but turn into standard.
Lang argues that can change, and as a view into the longer term, he and one other safety researcher, Andrew Hughes of Narf Industries, plan to display their very own Kubernetes rootkit on the Black Hat Europe Convention in December. “The actual change is the attackers studying that Kubernetes is more and more widespread within the cloud, and find out how to take care of it and find out how to get round it, and find out how to make use of it even,” he says.
Kubernetes Admins Want Visibility
Usually, a sufferer must see a rootkit getting loaded or a vulnerability being exploited by the attacker to catch an assault on a Kubernetes cluster, Lang says. Nonetheless, admins may look out for kernel modules that get loaded throughout runtime, which actually mustn’t occur in a manufacturing setting, he says.
“These programs do not actually do a complete lot of loopy stuff, so for those who see [kernel modules loading] inside a container or on host that runs containers, you could be fairly assured one thing unhealthy is occurring,” he says. “In any other case, catching it is extremely, very tough, as a result of lots of it occurs in consumer house or in an utility layer the place you do not have lots of deep perception.”
Admins also needs to ask their pink crew to conduct a bunch train, working in opposition to defenders to assault, after which with defenders to research the assault — a course of known as purple teaming.
Sysdig runs its personal honeypot, exposing Kubernetes ports to potential assaults, and usually, the primary probes come rapidly, Lang says.
“Inside minutes, generally seconds, it is already getting attacked,” he says. “So purple teaming is how you can find and shut your gaps, after which not placing Kubernetes on the Web within the first place is a good way to not get attacked.”


