A brand new variant of the Agent Tesla malware has been noticed delivered by way of a lure file with the ZPAQ compression format to reap information from a number of e-mail purchasers and practically 40 internet browsers.
“ZPAQ is a file compression format that provides a greater compression ratio and journaling operate in comparison with extensively used codecs like ZIP and RAR,” G Information malware analyst Anna Lvova stated in a Monday evaluation.
“That signifies that ZPAQ archives might be smaller, saving space for storing and bandwidth when transferring information. Nevertheless, ZPAQ has the most important drawback: restricted software program assist.”
First showing in 2014, Agent Tesla is a keylogger and distant entry trojan (RAT) written in .NET that is supplied to different risk actors as a part of a malware-as-a-service (MaaS) mannequin.
It is typically used as a first-stage payload, offering distant entry to a compromised system and utilized to obtain extra subtle second-stage instruments akin to ransomware.
Agent Tesla is often delivered by way of phishing emails, with latest campaigns leveraging a six-year-old reminiscence corruption vulnerability in Microsoft Workplace’s Equation Editor (CVE-2017-11882).
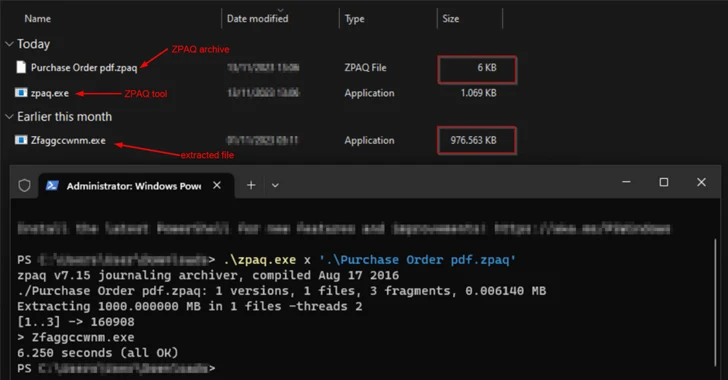
The most recent assault chain begins with an e-mail containing a ZPAQ file attachment that purports to be a PDF doc, opening which extracts a bloated .NET executable that is principally padded with zero bytes to artificially inflate the pattern measurement to 1 GB in an effort to bypass conventional safety measures.
“The principle operate of the unarchived .NET executable is to obtain a file with .wav extension and decrypt it,” Lvova defined. “Utilizing generally used file extensions disguises the visitors as regular, making it tougher for community safety options to detect and stop malicious exercise.”
The top aim of the assault is to contaminate the endpoint with Agent Teslathat’s obfuscated with .NET Reactor, a respectable code safety software program. Command-and-control (C2) communications is completed by way of Telegram.
The event is an indication that risk actors are experimenting with unusual file codecs for malware supply, necessitating that customers be looking out for suspicious emails and hold their methods up-to-date.
“The utilization of the ZPAQ compression format raises extra questions than solutions,” Lvova stated. “The assumptions listed here are that both risk actors goal a particular group of people that have technical data or use much less extensively identified archive instruments, or they’re testing different strategies to unfold malware sooner and bypass safety software program.”