A brand new Phobos ransomware variant frames the favored VX-Underground malware-sharing collective, indicating the group is behind assaults utilizing the encryptor.
Phobos launched in 2018 in what’s believed to be a ransomware-as-a-service derived from the Crysis ransomware household. As a part of this operation, a gaggle of menace actors handle the event of the ransomware and maintain the grasp decryption key, whereas different menace actors act as associates to breach networks and encrypt units.
Whereas Phobos has been round for a very long time, it by no means advanced into an “elite” operation recognized for conducting large assaults and demanding thousands and thousands of {dollars}.
Nevertheless, that doesn’t imply it’s not a giant operation, because it sees extensive distribution by many affiliated menace actors and accounts for 4% of all submissions to the ID Ransomware service in 2023.
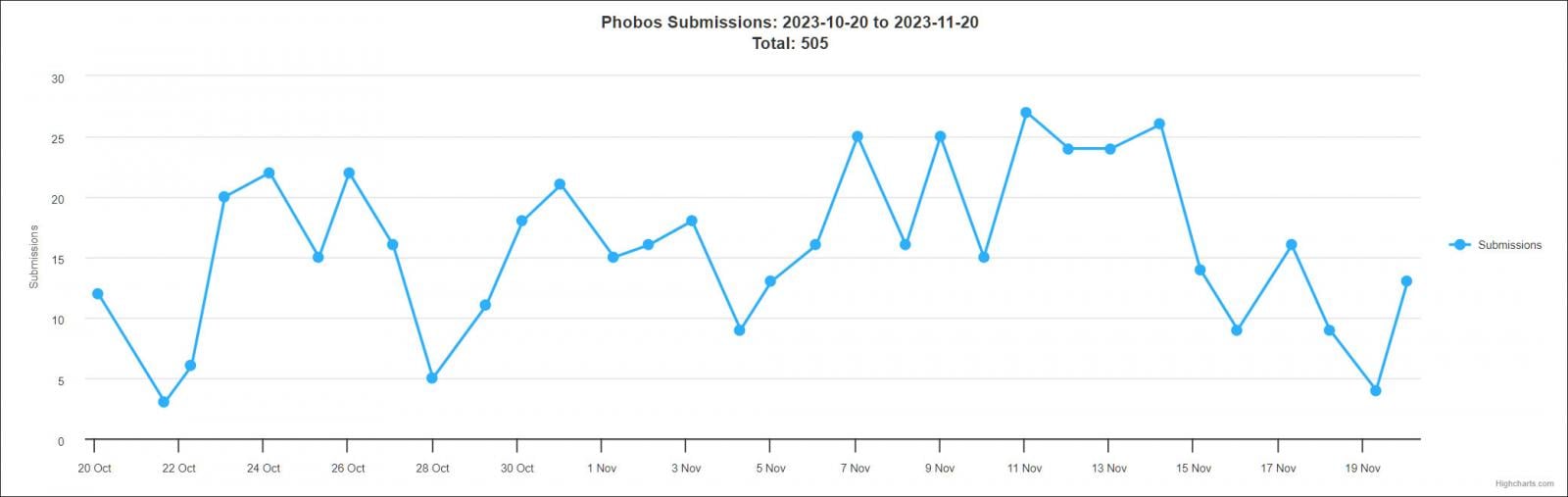
Supply: ID Ransomware
Framing VX
In the present day, ransomware hunter PCrisk discovered a brand new variant of the Phobos ransomware that makes an attempt to body the VX-Underground group.
When encrypting recordsdata, the malware will append the .id[[unique_id].[staff@vx-underground.org].VXUG string, with the e-mail being professional and the ultimate extension ‘VXUG,’ standing for VX-Underground.
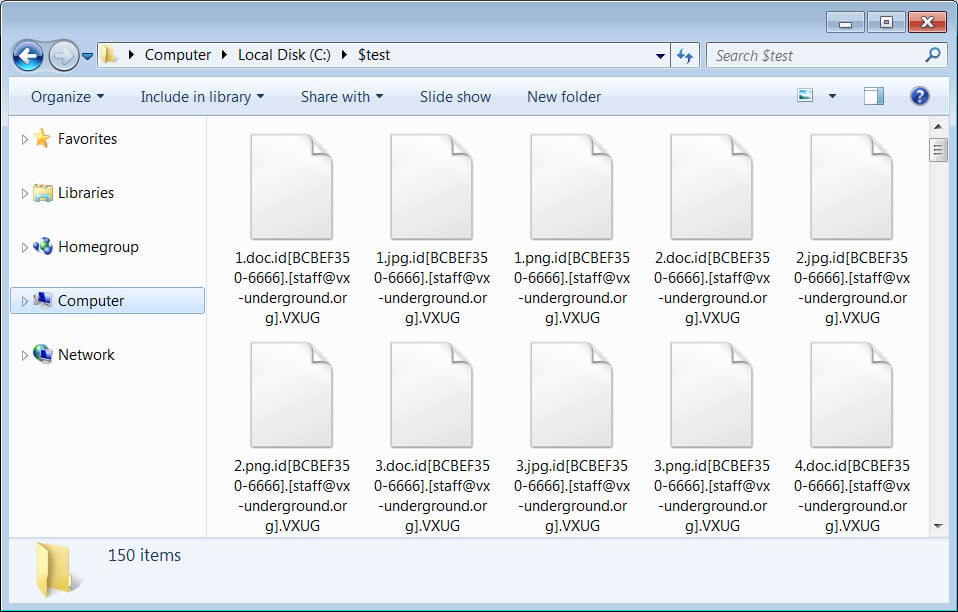
Supply: BleepingComputer
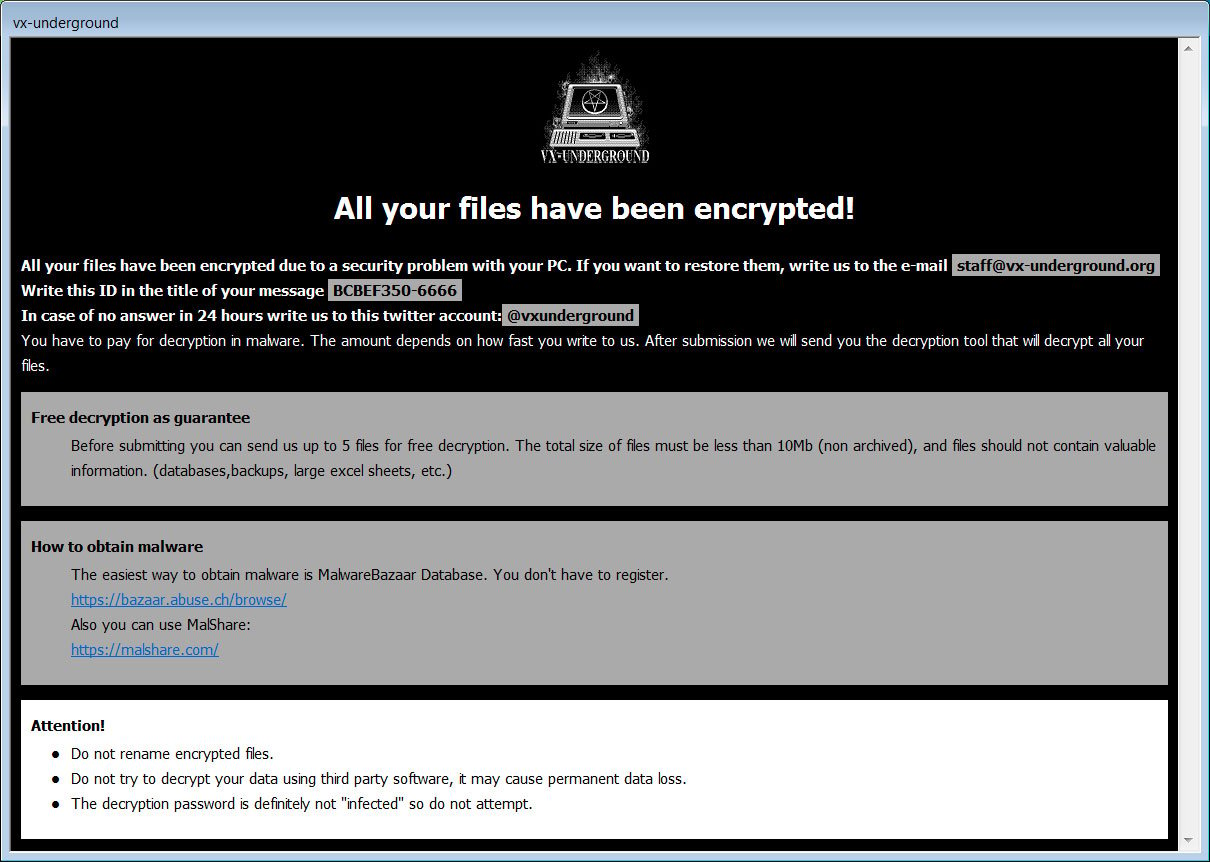
When completed, Phobos will create two ransom notes on the Home windows Desktop and elsewhere.
The primary is a textual content ransom notice named ‘Purchase Black Mass Quantity II.txt,’ which pokes some enjoyable at VX by saying that the decryption password is just not “contaminated,” the password used on all VX malware archives.
“!!! All your recordsdata are encrypted !!!
To decrypt them ship e-mail to this tackle: employees@vx-underground.org.
If we do not reply in 48h., ship message to this twitter: @vxunderground
and no the decryption password is just not “contaminated””
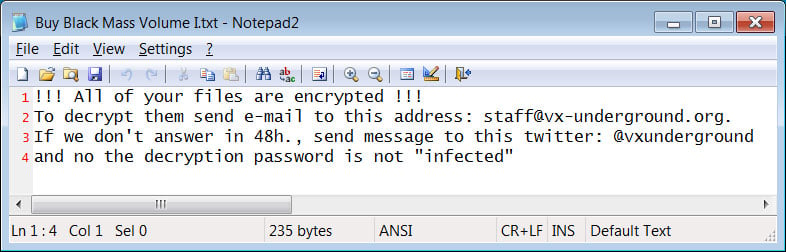
Supply: BleepingComputer
The second is an HTA file named ‘Purchase Black Mass Quantity II.hta,’ your customary Phobos ransom notice personalized to make the most of the VX-Underground emblem, identify, and get in touch with data. Black Mass are books written by the VX-Underground and offered on Amazon.
Supply: BleepingComputer
Watching the watchers
Like safety researchers, menace actors are concerned within the on-line infosec and cybersecurity communities, actively taking part in discussions or quietly watching from the sidelines. This monitoring, although, has led to related taunts being added to malware and ransomware up to now.
For instance, when REvil’s precursor, GandCrab, was launched, the menace actors named their command and management servers after BleepingComputer, Emsisoft, ESET, and NoMoreRansom.
Whereas that was a good-natured taunting of these concerned in ransomware monitoring and analysis, different examples took a darker flip.
In 2016, the developer of the Apocalypse ransomware started embedding abusive feedback about ransomware skilled Fabian Wosar in its ‘Fabiansomware’ encryptors out of frustration that Wosar saved discovering weaknesses within the encryption.
In 2020, a developer for the Maze ransomware created a knowledge wiper/MBR Locker named after the late safety researcher Vitali Kremez and Sentinel One.
The Maze developer instructed BleepingComputer after they launched the decryption keys that they distributed the wiper to harass Kremez, who has been posting destructive tweets concerning the ransomware operation.
Extra lately, ransomware generally known as ‘Azov Ransomware” was closely distributed by pirated software program, key turbines, and adware bundles worldwide.
This ransomware claimed to have been created on my own, BleepingComputer, Hasherazade, MalwareHunterTeam, Michael Gillespie, and Vitali Kremez, telling victims to contact us for a decryption key.
For many who work together with malware builders, you all the time run the danger of being included in one among their tasks.
Whereas the taunting is usually good-natured, in some instances, like we noticed with Azov and the Kremez Wiper, it could get a bit nasty.


