
MySQL servers are being focused by the ‘Ddostf’ malware botnet to enslave them for a DDoS-as-a-Service platform whose firepower is rented to different cybercriminals.
This marketing campaign was found by researchers on the AhnLab Safety Emergency Response Middle (ASEC) throughout their common monitoring of threats concentrating on database servers.
ASEC stories that Ddostf’s operators both leverage vulnerabilities in unpatched MySQL environments or brute-force weak administrator account credentials to breach the servers.
Exploitation of UDF
The attackers are scanning the web for uncovered MySQL servers and, when discovered, try to breach them by brute-forcing administrator credentials.
For Home windows MySQL servers, the menace actors use a characteristic known as user-defined capabilities (UDFs) to execute instructions on the breached system.
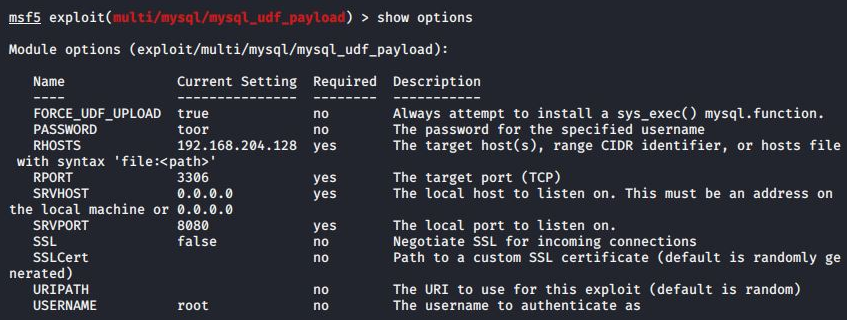
UDF is a MySQL characteristic that enables customers to outline capabilities in C or C++ and compile them right into a DLL (dynamic hyperlink library) file that extends the capabilities of the database server.
The attackers, on this case, create their very own UDFs and register them with the database server as a DLL file (amd.dll) with the next malicious capabilities:
- Downloading payloads just like the Ddostf DDoS bot from a distant server.
- Executing arbitrary system-level instructions despatched by the attackers.
- Output the outcomes of command execution to a brief file and ship them to the attackers.
The UDF abuse facilitates loading the first payload of this assault, the Ddostf bot consumer.
Nevertheless, it might probably additionally probably enable different malware set up, information exfiltration, creation of backdoors for persistent entry, and extra.
Ddostf particulars
Ddostf is a malware botnet of Chinese language origin, first noticed within the wild roughly seven years in the past, and targets each Linux and Home windows techniques.
On Home windows, it establishes persistence by registering itself as a system service upon first working after which decrypts its C2 (command and management) configuration to determine a connection.
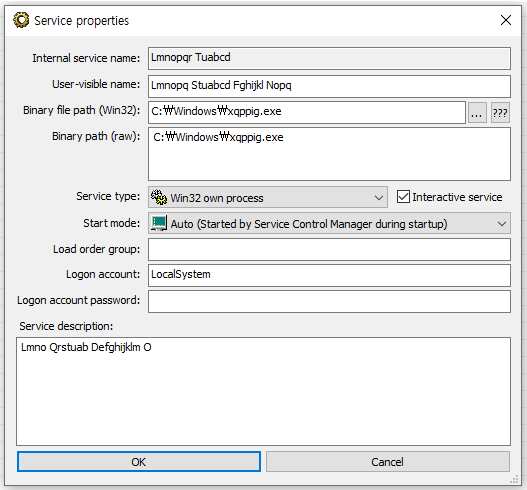
The malware profiles the host system and sends information equivalent to CPU frequency and variety of cores, language data, Home windows model, community velocity, and so on., to its C2.
The C2 server might ship DDoS assault instructions to the botnet consumer, together with SYN Flood, UDP Flood, and HTTP GET/POST Flood assault varieties, request to cease transmitting system standing information, swap to a brand new C2 deal with, or obtain and execute a brand new payload.
ASEC feedback that Ddostf’s skill to hook up with a brand new C2 deal with makes it stand out from most DDoS botnet malware and is a component that offers it resilience in opposition to takedowns.
The cybersecurity firm means that MySQL admins apply the most recent updates and decide lengthy, distinctive passwords to guard admin accounts from brute pressure and dictionary assaults.


