Government abstract
Multifactor authentication, or MFA, offers customers with an added layer of safety when logging into internet functions. Surpassing its predecessor, two-factor authentication, in 2023, MFA is a regular choice for one more layer of safety for on-line accounts. .
In Might 2022, the Cybersecurity & Infrastructure Safety Company (CISA) revealed safety advisory AA22-074A describing how default configurations inside MFA functions are thought of a vulnerability. The tactic was utilized by Russian state-sponsored cyber actors as early as Might 2021 in a profitable compromise of a US group.
Primarily based on this steering from CISA, the AT&T Cybersecurity managed detection and response (MDR) safety operations heart (SOC) proactively scanned throughout our buyer fleet and found a buyer that was utilizing the default configuration, which could be exploited. SOC analysts contacted the client to tell them concerning the danger and supplied suggestions on tips on how to safe their community.
Investigation
Occasions search
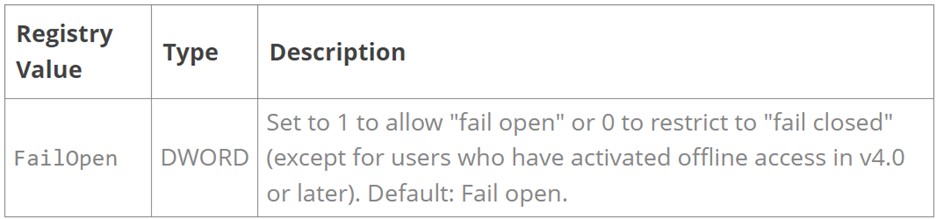
Analysts used the open-source software, Elastic Stack, to look our prospects for “FailOpen,”which is the default configuration inside MFA functions that makes unauthorized entry attainable.

Occasion deep-dive
The search revealed a buyer with their MFA utility set to FAILOPEN = 1, which is the setting that enables for a malicious actor to bypass authentication when exploited. The “FailOpen” setting permits for an incorrect try at a connection, which might then allow unfettered entry to an account with this setting on the client community.
Reviewing for added indicators
From there, SOC analysts pivoted to looking the client setting for any info that might determine related buyer property and accounts and that might point out outwardly malicious exercise. They found that the consumer accountable was listed as an administrator inside the buyer setting.
Response
Constructing the investigation
The analysts opened an investigation to handle the misconfiguration within the MFA cellular utility in addition to to substantiate whether or not or not the exercise related to the recognized consumer was approved. Included within the investigation was a proof of the vulnerability in addition to a abstract of the concerned consumer’s exercise on the recognized property during the last 30 days.
Buyer interplay
Analysts created a low-severity investigation, which on this case meant that they weren’t required to contact the client. (Our MDR prospects decide when and the way the SOC communicates with them.)
Nevertheless, to make sure that the difficulty was addressed in a well timed method, the analysts additionally notified the client’s assigned risk hunter group, “The ForCE,” and the investigation was reviewed and addressed by the client.
In the end, the investigation didn’t uncover any malicious occasions regarding the misconfiguration, nevertheless it illustrates how the AT&T MDR SOC will not be solely reactive but additionally works proactively to guard our prospects.