
Malicious actors have been abusing Ethereum’s ‘Create2’ perform to bypass pockets safety alerts and poison cryptocurrency addresses, which led to stealing $60,000,000 price of cryptocurrency from 99,000 individuals in six months.
That is reported by Web3 anti-scam specialists at ‘Rip-off Sniffer,’ who noticed a number of instances of in-the-wild exploitation of the perform, in some instances losses incurred by one particular person reaching as much as $1.6 million.
Authentic perform
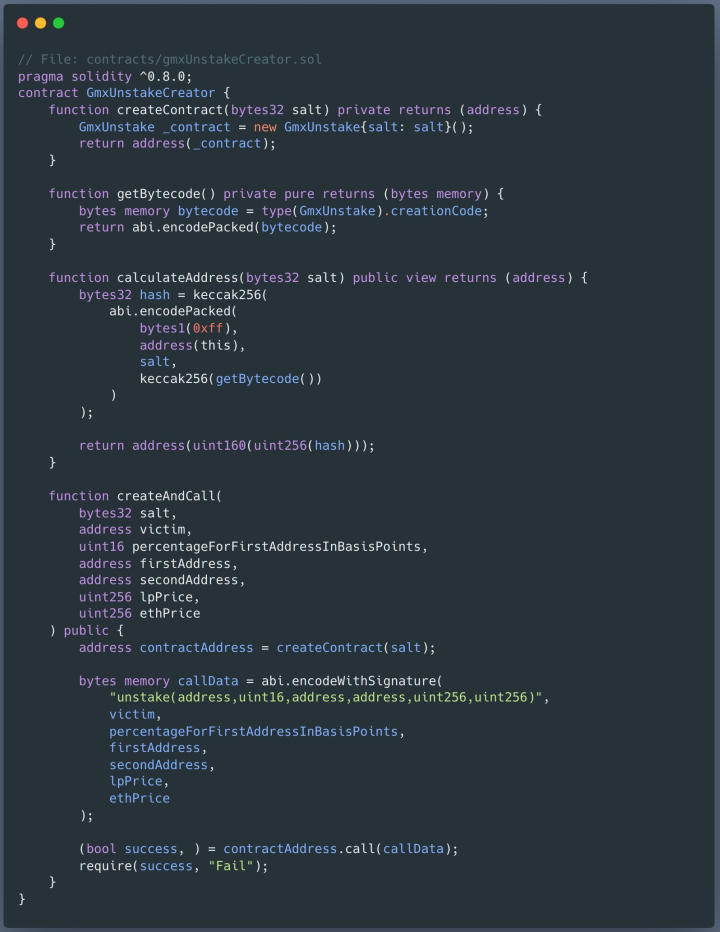
Create2 is an opcode in Ethereum, launched within the ‘Constantinople’ improve, that enables creating good contracts on the blockchain.
Not like the unique Create opcode, which generated new addresses primarily based on the creator’s deal with and nonce, Create2 permits calculating addresses earlier than the deployment of the contract.
It is a highly effective software for Ethereum builders, enabling superior and versatile contract interactions, parameter-based contract deal with pre-calculation, deployment flexibility, suitability for off-chain transactions and sure dApps.
Create2 launched important advantages, however a number of safety implications and new assault vectors additionally got here together with them.
Create2 opcode abuse
Rip-off Sniffer’s report explains that Create2 may be abused to generate contemporary contract addresses with no historical past of malicious/reported transactions, therefore bypassing pockets safety alerts.
When a sufferer indicators a malicious transaction, the attacker deploys a contract on the pre-calculated deal with and transfers the sufferer’s belongings to it, a non-reversible course of.
In a current case analysts noticed, a sufferer misplaced $927,000 price of GMX after they had been tricked into signing a switch contract that despatched the belongings to a pre-computed deal with.
The second kind of Create2 abuse is producing addresses just like official ones owned by the recipient, thus tricking customers into sending belongings to the risk actors, pondering they’re sending it to a recognized deal with.
The scheme, which is known as ‘deal with poisoning,’ entails producing numerous addresses after which choosing those who match their particular phishing wants every time to trick their targets.
Since August 2023, Rip-off Sniffer has recorded 11 victims dropping almost $3 million, with considered one of them transferring $1.6 million to an deal with resembling one they’d despatched cash to just lately.
Most of those assaults went beneath the radar, silently siphoning thousands and thousands, however some have caught the eye of the neighborhood.
Firstly of the 12 months, MetaMask warned about scammers utilizing freshly-generated addresses that match these utilized by the sufferer in current transactions.
Within the rip-off, the risk actor might also ship the sufferer a small quantity in crypto to register the deal with within the pockets’s historical past, thus rising the possibilities of the sufferer making the cost.
In early August 2023, a Binance operator mistakenly despatched $20 million to scammers who employed the ‘deal with poisoning’ trick however seen the error shortly and froze the recipient’s deal with.
Notably, utilizing lookalike cryptocurrency addresses is a trick seen in clipboard-hijacking malware instruments, just like the Laplas Clipper, highlighting the strategy’s effectiveness.
When performing cryptocurrency transactions, it’s at all times really useful to examine the recipient’s deal with completely, and never simply the primary and final three-four characters, earlier than approving it.


