
The operator of the Nokoyawa ransomware-as-a-service (RaaS), a risk actor often called ‘farnetwork’, constructed expertise over time by serving to the JSWORM, Nefilim, Karma, and Nemty affiliate applications with malware growth and operation administration.
A report from cybersecurity firm Group-IB supplies perception into farnetwork’s exercise and the way they regularly constructed their profile as a extremely energetic participant within the ransomware enterprise.
In interactions with risk intelligence analysts, farnetwork shared helpful particulars that hyperlink them to ransomware operations beginning 2019 and a botnet with entry to a number of company networks.
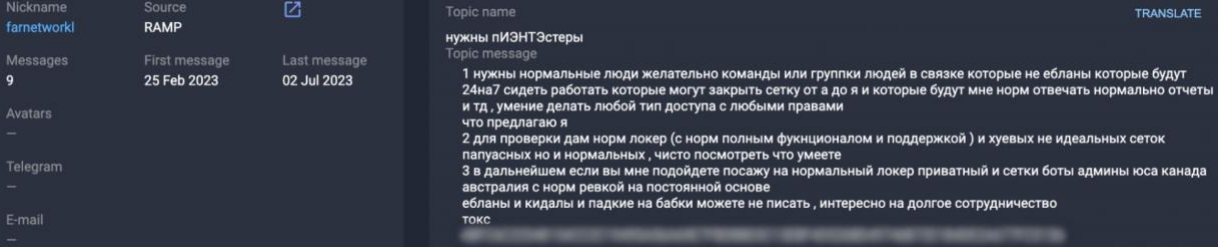
Based on a report Group-IB shared with BleepingComputer, the risk actor has a number of usernames (e.g. farnetworkl, jingo, jsworm, razvrat, piparkuka, and farnetworkitand) and has been energetic on a number of Russian-speaking hacker boards attempting to recruit associates for varied ransomware operations.

In March, although, farnetwork began on the lookout for associates for his or her ransomware-as-a-service program primarily based on the Nokoyawa locker. Nonetheless, Group-IB’s risk intelligence analysts say that the actor made it clear that they weren’t concerned within the growth of Nokoyawa.
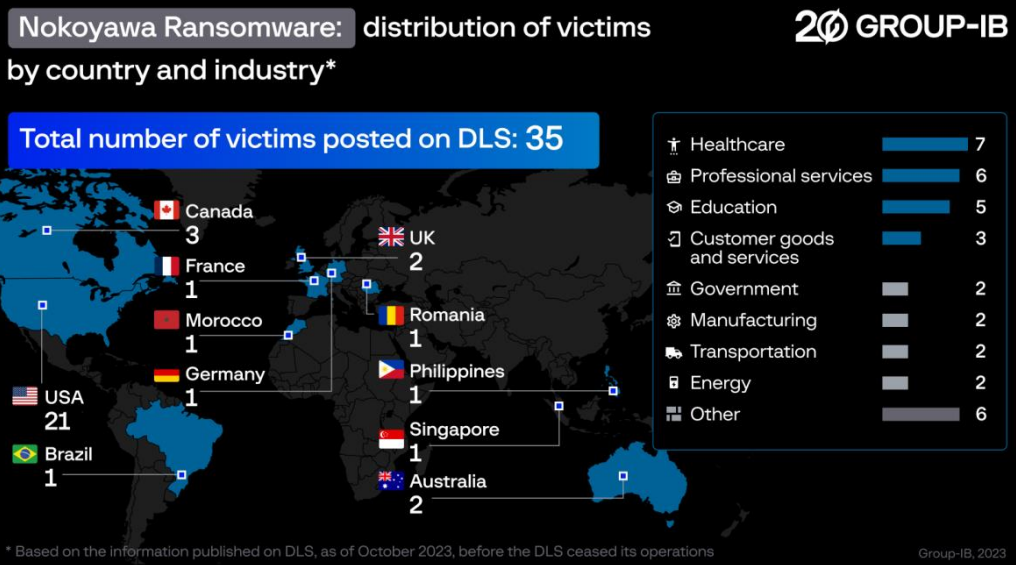
Working the RaaS enterprise did not final very lengthy as farnetwork introduced lately that they’d retire from the scene and in October they shut down the Nokoyawa RaaS program, after leaking information of 35 victims.
Nonetheless, Group-IB believes that this transfer is a part of the risk actor’s technique to lose their tracks and begin afresh underneath a brand new model
Operations supervisor
In Nokoyawa ransomware, farnetwork acted as a challenge chief, affiliate recruiter, promoter of the RaaS on darknet boards, and botnet supervisor.
The botnet enabled associates direct entry to already compromised networks. For this perk, they’d pay the botnet proprietor 20% from the collected ransom and the ransomware proprietor would get 15%.
A 65% reduce for the ransomware affiliate could appear to be a nasty deal, contemplating that different applications pay as much as 85% of the ransom, however the price lined the hassle of discovering an acceptable goal and breaching it.
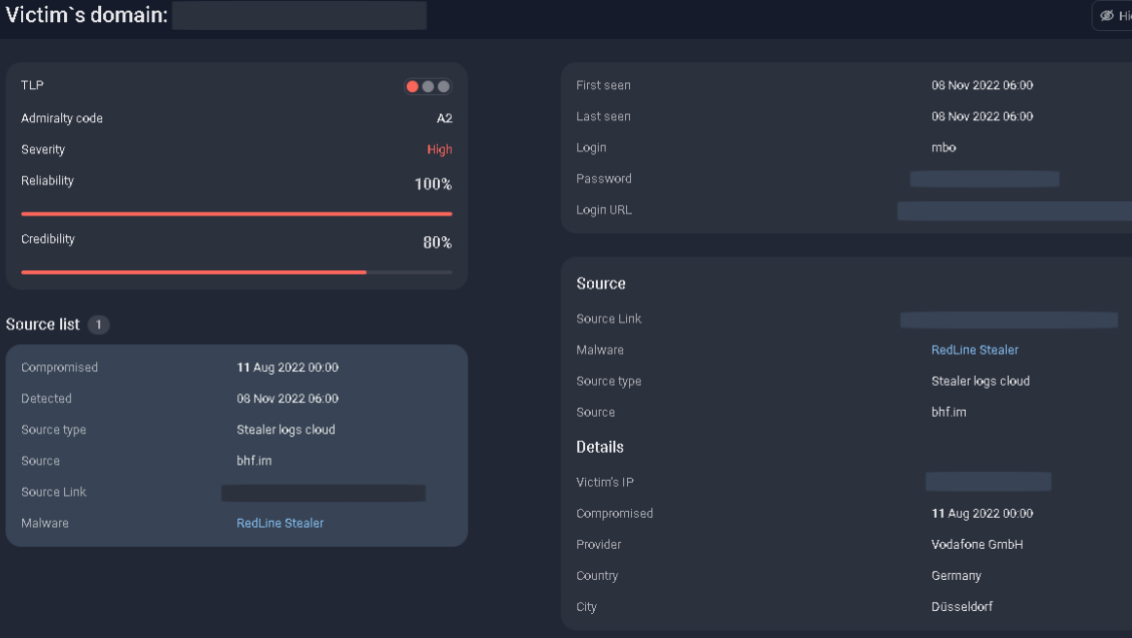
Farnetwork examined affiliate candidates by offering them with a number of company account credentials sourced from the Underground Cloud of Logs (UCL) service, which sells logs stolen by info-stealers corresponding to RedLine, Vidar, and Raccoon.
The associates had been anticipated to escalate their privileges on the community, steal recordsdata, run the encryptor, and demand a ransom cost.
Timeline of previous actions
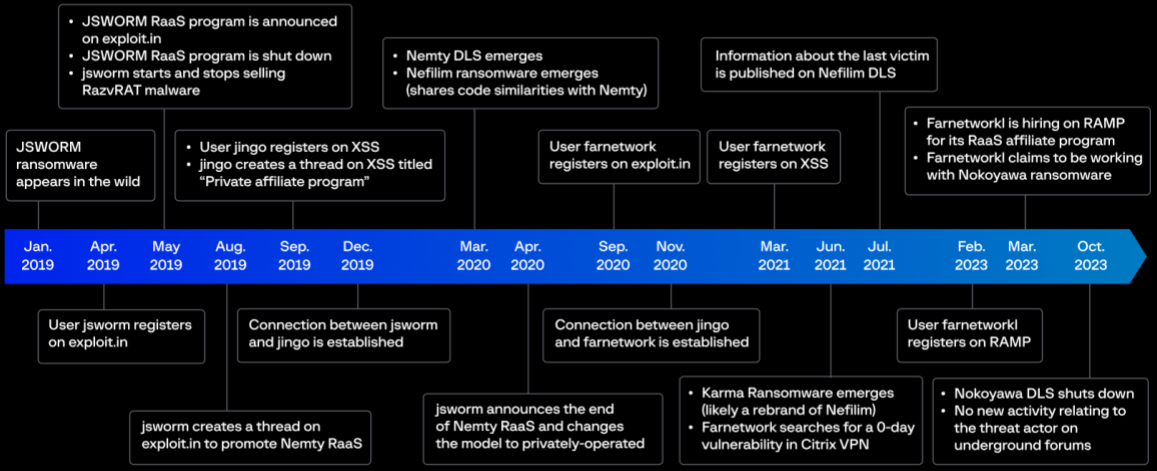
Group-IB has been capable of monitor farnetwork’s actions way back to January 2019 and located connections to the JSWORM, Nemty, Nefilim, and Karma ransomware strains.
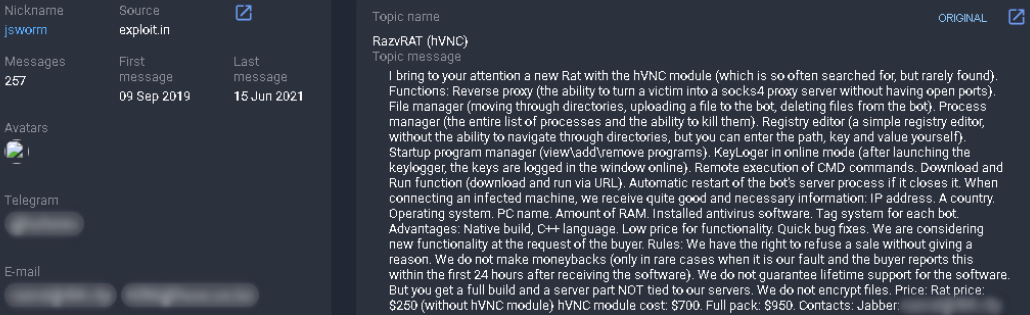
In April 2019, farnetwork promoted the JSWORM RaaS program on the Exploit hacker discussion board, the place the risk actor marketed the RazvRAT malware.
In August 2019, after JSWORM shut down, the risk actor switched to selling Nemty on at the very least two Russian-speaking underground boards.
In March 2020, Nefilim ransomware emerged as a brand new associates program with a knowledge leak web site referred to as Company Leaks. The subsequent month, farnetwork introduced that Nemty would go non-public.

In June 2021, a seemingly rebrand of Nefilim referred to as Karma appeared, and in July 2021, Nefilim went silent. Throughout that point, farnetwork was looking for details about a zero-day vulnerability in Citrix VPN.
In February 2023, farnetwork pivoted to the RAMP discussion board saying they had been working with the Nokoyawa ransomware as a recruiter and entry supervisor.
Based mostly on Group-IB’s findings, farnetwork is suspected to have been concerned in creating or at the very least within the evolution and administration of the talked about ransomware strains. The strongest ties are with Nefilim and Karma, each thought-about evolutions of Nemty.
Group-IB managed to attach the completely different usernames to the identical risk actor, displaying that ransomware operations can come and go however behind them are seasoned people that preserve the enterprise going underneath new names.


