A brand new variant of the GootLoader malware known as GootBot has been discovered to facilitate lateral motion on compromised techniques and evade detection.
“The GootLoader group’s introduction of their very own customized bot into the late levels of their assault chain is an try and keep away from detections when utilizing off-the-shelf instruments for C2 equivalent to CobaltStrike or RDP,” IBM X-Power researchers Golo Mühr and Ole Villadsen stated.
“This new variant is a light-weight however efficient malware permitting attackers to quickly unfold all through the community and deploy additional payloads.”
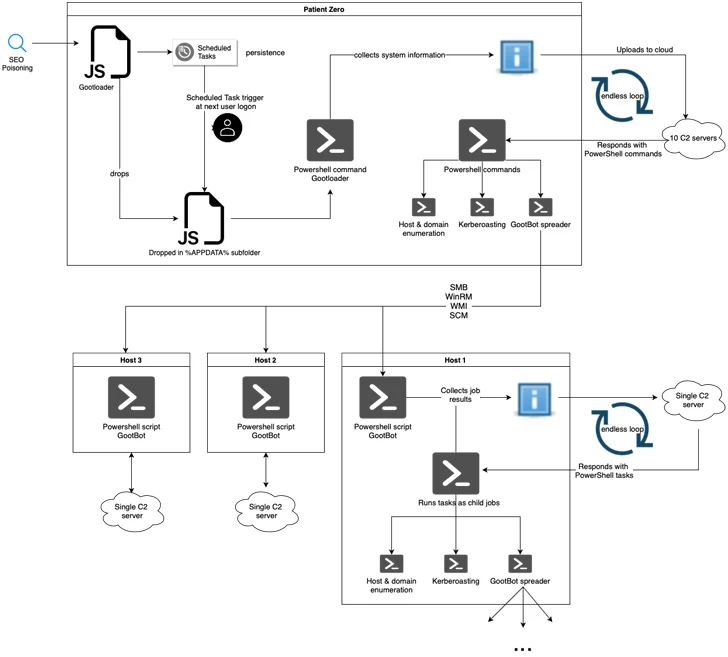
GootLoader, because the title implies, is a malware able to downloading next-stage malware after luring potential victims utilizing SEO (Search engine optimisation) poisoning techniques. It is linked to a menace actor tracked as Hive0127 (aka UNC2565).
The usage of GootBot factors to a tactical shift, with the implant downloaded as a payload after a Gootloader an infection in lieu of post-exploitation frameworks equivalent to CobaltStrike.
Described as an obfuscated PowerShell script, GootBot is designed to hook up with a compromised WordPress web site for command and management and obtain additional instructions.
Complicating issues additional is using a novel hard-coded C2 server for every deposited GootBot pattern, making it tough to dam malicious visitors.
“At present noticed campaigns leverage Search engine optimisation-poisoned searches for themes equivalent to contracts, authorized kinds, or different business-related paperwork, directing victims to compromised websites designed to seem like reliable boards the place they’re tricked into downloading the preliminary payload as an archive file,” the researchers stated.
The archive file incorporates an obfuscated JavaScript file, which, upon execution, fetches one other JavaScript file that is triggered by way of a scheduled job to attain persistence.
Within the second stage, JavaScript is engineered to run a PowerShell script for gathering system info and exfiltrating it to a distant server, which, in flip, responds with a PowerShell script that is run in an infinite loop and grants the menace actor to distribute numerous payloads.
This contains GootBot, which beacons out to its C2 server each 60 seconds to fetch PowerShell duties for execution and transmit the outcomes of the execution again to the server within the type of HTTP POST requests.
A few of the different capabilities of GootBot vary from reconnaissance to finishing up lateral motion throughout the surroundings, successfully increasing the size of the assault.
“The invention of the Gootbot variant highlights the lengths to which attackers will go to evade detection and function in stealth,” the researchers stated. “This shift in TTPs and tooling heightens the danger of profitable post-exploitation levels, equivalent to GootLoader-linked ransomware affiliate exercise.”