The highest-level area for the US — .US — is house to 1000’s of newly-registered domains tied to a malicious hyperlink shortening service that facilitates malware and phishing scams, new analysis suggests. The findings come shut on the heels of a report that recognized .US domains as among the many most prevalent in phishing assaults over the previous yr.
Researchers at Infoblox say they’ve been monitoring what seems to be a three-year-old hyperlink shortening service that’s catering to phishers and malware purveyors. Infoblox discovered the domains concerned are sometimes three to seven characters lengthy, and hosted on bulletproof internet hosting suppliers that cost a premium to disregard any abuse or authorized complaints. The brief domains don’t host any content material themselves, however are used to obfuscate the actual handle of touchdown pages that attempt to phish customers or set up malware.
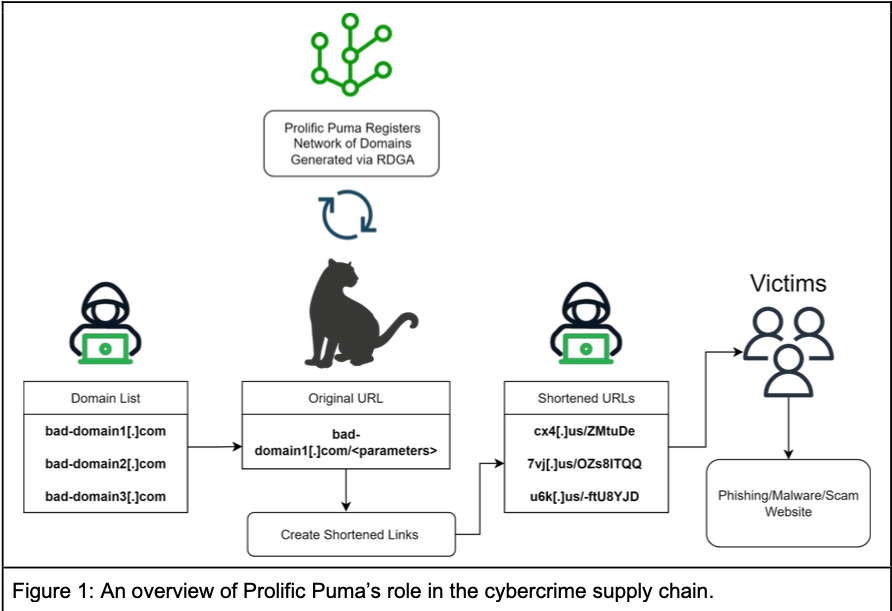
A graphic describing the operations of a malicious hyperlink shortening service that Infoblox has dubbed “Prolific Puma.”
Infoblox says it’s unclear how the phishing and malware touchdown pages tied to this service are being initially promoted, though they think it’s primarily via scams focusing on individuals on their telephones by way of SMS. A brand new report says the corporate mapped the contours of this hyperlink shortening service thanks partly to pseudo-random patterns within the brief domains, which all seem on the floor to be a meaningless jumble of letters and numbers.
“This got here to our consideration as a result of we’ve methods that detect registrations that use area title technology algorithms,” stated Renee Burton, head of menace intelligence at Infoblox. “We’ve got not discovered any reliable content material served via their shorteners.”
Infoblox decided that till Might 2023, domains ending in .information accounted for the majority of latest registrations tied to the malicious hyperlink shortening service, which Infoblox has dubbed “Prolific Puma.” Since then, they discovered that whoever is accountable for working the service has used .US for roughly 55 p.c of the full domains created, with a number of dozen new malicious .US domains registered each day.
.US is overseen by the Nationwide Telecommunications and Info Administration (NTIA), an government department company of the U.S. Division of Commerce. However Uncle Sam has lengthy outsourced the administration of .US to numerous non-public firms, which have progressively allowed the US’s top-level area to devolve right into a cesspool of phishing exercise.
Or so concludes The Interisle Consulting Group, which gathers phishing information from a number of trade sources and publishes an annual report on the newest developments. Way back to 2018, Interisle discovered .US domains had been the worst on the planet for spam, botnet (assault infrastructure for DDOS and so on.) and illicit or dangerous content material.
Interisle’s latest research examined six million phishing studies between Might 1, 2022 and April 30, 2023, and recognized roughly 30,000 .US phishing domains. Interisle discovered vital numbers of .US domains had been registered to assault a number of the United States’ most outstanding firms, together with Financial institution of America, Amazon, Apple, AT&T, Citi, Comcast, Microsoft, Meta, and Goal. Others had been used to impersonate or assault U.S. authorities companies.
Beneath NTIA laws, area registrars processing .US area registrations should take sure steps (PDF) to confirm that these prospects really reside in the US, or else personal organizations based mostly within the U.S. Nevertheless, if one registers a .US area via GoDaddy — the most important area registrar and the present administrator of the .US contract — the best way one “proves” their U.S. nexus is just by selecting from one in every of three pre-selected affirmative responses.
In an age when most area registrars are mechanically redacting buyer data from publicly accessible registration data to keep away from working afoul of European privateness legal guidelines, .US has remained one thing of an outlier as a result of its constitution specifies that every one registration data be made public. Nevertheless, Infoblox stated it discovered greater than 2,000 malicious hyperlink shortener domains ending in .US registered since October 2023 via NameSilo which have one way or the other subverted the transparency necessities for the usTLD and transformed to non-public registrations.
“By way of our personal expertise with NameSilo, it’s not doable to pick out non-public registration for domains within the usTLD via their interface,” Infoblox wrote. “And but, it was accomplished. Of the full domains with non-public data, over 99% had been registered with NameSilo. Right now, we aren’t capable of clarify this habits.”
NameSilo CEO Kristaps Ronka stated the corporate actively responds to studies about abusive domains, however that it hasn’t seen any abuse studies associated to Infoblox’s findings.
“We take down lots of to 1000’s of domains, a lot of them proactively to fight abuse,” Ronka stated. “Our present abuse price on abuseIQ for instance is at the moment at 0%. AbuseIQ receives studies from numerous sources and we’re but to see these ‘Puma’ abuse studies.”
Specialists who monitor domains related to malware and phishing say even phony data equipped at registration is helpful in figuring out probably malicious or phishous domains earlier than they can be utilized for abuse.
For instance, when it was registered via NameSilo in July 2023, the area 1ox[.]us — like 1000’s of others — listed its registrant as “Leila Puma” at a road handle in Poland, and the e-mail handle blackpumaoct33@ukr.internet. However in accordance with DomainTools.com, on Oct. 1, 2023 these data had been redacted and hidden by NameSilo.
Infoblox notes that the username portion of the e-mail handle seems to be a reference to the music October 33 by the Black Pumas, an Austin, Texas based mostly psychedelic soul band. The Black Pumas aren’t precisely a family title, however they did just lately have a well-liked Youtube video that featured a canopy of the Kinks music “Strangers,” which included an emotional visible narrative about Ukrainians searching for refuge from the Russian invasion, titled “Ukraine Strangers.” Additionally, Leila Puma’s e-mail handle is at a Ukrainian e-mail supplier.
DomainTools reveals that lots of of different malicious domains tied to Prolific Puma beforehand had been registered via NameCheap to a “Josef Bakhovsky” at a distinct road handle in Poland. Based on ancestry.com, the anglicized model of this surname — Bakovski — is the standard title for somebody from Bakowce, which is now referred to as Bakivtsi and is in Ukraine.
This doable Polish and/or Ukrainian connection could or could not inform us one thing in regards to the “who” behind this hyperlink shortening service, however these particulars are helpful for figuring out and grouping these malicious brief domains. Nevertheless, even this meager visibility into .US registration information is now beneath menace.
The NTIA just lately printed a proposal that will permit registrars to redact all registrant information from WHOIS registration data for .US domains. A broad array of trade teams have filed feedback opposing the proposed adjustments, saying they threaten to take away the final vestiges of accountability for a top-level area that’s already overrun with cybercrime exercise.
Infoblox’s Burton says Prolific Puma is outstanding as a result of they’ve been capable of facilitate malicious actions for years whereas going largely unnoticed by the safety trade.
“This exposes how persistent the prison financial system might be at a provide chain stage,” Burton stated. “We’re all the time wanting on the finish malware or phishing web page, however what we’re discovering right here is that there’s this center layer of DNS menace actors persisting for years with out discover.”
Infoblox’s full report on Prolific Puma is right here.


