A excessive profile French basketball group has fallen sufferer to the NoEscape ransomware-as-a-service group, who declare to have stolen 32 GB of knowledge together with delicate private details about the membership’s star gamers.
Lyon-based ASVEL, owned by former NBA star Tony Parker, has issued a press launch confirming rumours that unfold earlier this month that it had been hacked.
ASVEL says that the primary it knew of a possible safety breach was on October 12 when it was approached by members of the press who had noticed references to a hack of the basketball membership on NoEscape’s darkish net leak website.
We’ve got 32GB of knowledge reminiscent of:
Gamers’ private knowledge!
Passports and ID playing cards!
Finance, taxes, insurance coverage, price range, banking. authorized paperwork, studies, confidential letters!
Contracts for looking for gamers in addition to confidential agreements and contracts, NDA!
Consumer paperwork and letters, in addition to tens of 1000’s of different confidential and vital paperwork stolen out of your servers and PCs.
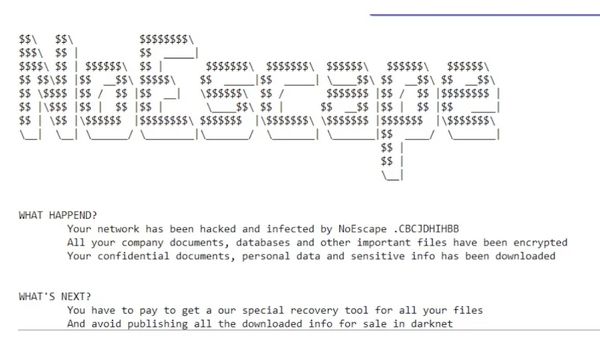
NoEscape is threatening to publish the stolen knowledge until ASVEL is ready to barter a ransom fee. The cybercriminal group says that it has emailed directions to the membership about how negotiations can start:
We advise the LDLC ASVEL administration to make the correct choice and call us. In any other case, if you don’t contact us, all knowledge will likely be revealed and the storm of issues that can await you can be damaging!!! Letters with directions have been despatched to your company emails, use them and we’ll assist you to resolve this drawback. Assign an individual to the place of negotiator, and inform him to contact us, we’ll clarify every thing and assist you to resolve this drawback. Time is working out.
ASVEL, which has introduced in third-party specialists to assist with its response to the ttack, says that its membership actions haven’t been disrupted, and that – to date – it has not seen proof that followers’ fee info has been compromised.
The NoEscape ransomware first appeared in Might 2023. It’s typically believed to be a successor to the Avaddon ransomware group that was disbanded in 2021, and has just lately been within the information after warnings had been issued in regards to the gang’s focusing on of the healthcare sector.
The NoEscape ransomware group seems to not be eager on focusing on organisations primarily based in former Soviet nations, providing a free decryptor if corporations inside Russia’s sphere of affect are breached. One imagines that the operators of the ransomware have adopted this coverage in an try to scale back the possibilities that they may discover themselves at odds with native legislation enforcement companies.


