Vital safety flaws have been disclosed within the Open Authorization (OAuth) implementation of fashionable on-line providers corresponding to Grammarly, Vidio, and Bukalapak, constructing upon earlier shortcomings uncovered in Reserving[.]com and Expo.
The weaknesses, now addressed by the respective corporations following accountable disclosure between February and April 2023, may have allowed malicious actors to acquire entry tokens and doubtlessly hijack consumer accounts.
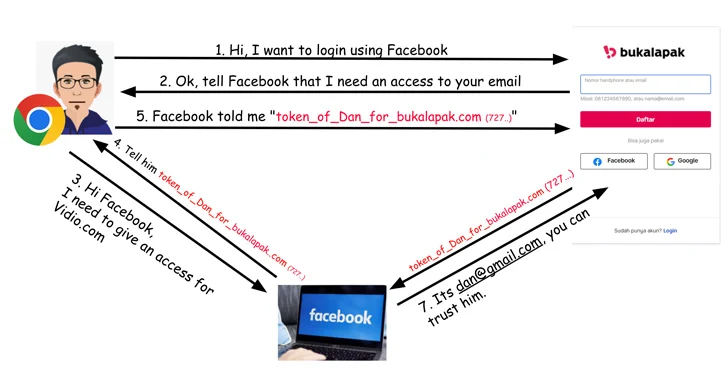
OAuth is a commonplace that is generally used as a mechanism for cross-application entry, granting web sites or purposes entry to their info on different web sites, corresponding to Fb, however with out giving them the passwords.
“When OAuth is used to supply service authentication, any safety breach in it might probably result in identification theft, monetary fraud, and entry to numerous private info together with bank card numbers, personal messages, well being data, and extra, relying on the particular service being attacked,” Salt Safety researcher Aviad Carmel mentioned.
The issue recognized in Vidio stems from an absence of token verification, which means an attacker can use an entry token generated for one more App ID, a random identifier created by Fb for each software or web site that will get registered in its developer portal.
In a possible assault state of affairs, a menace actor may create a rogue web site that provides a sign-in possibility by means of Fb to gather the entry tokens and subsequently use them in opposition to Vidio.com (which has the App ID 92356), thereby permitting full account takeover.
The API safety agency mentioned it additionally found the same problem with token verification on Bukalapak.com by way of Fb login that might end in unauthorized account entry.
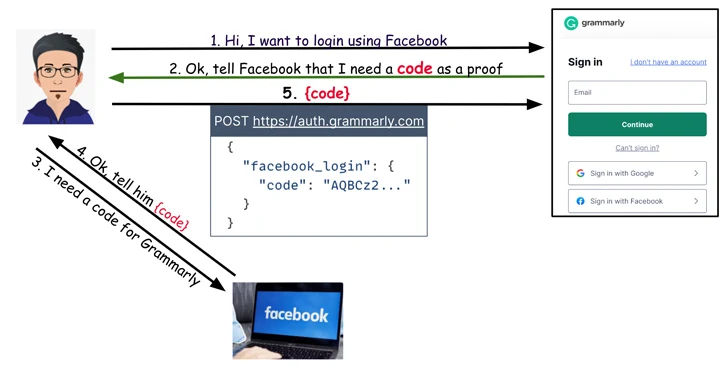
On Grammarly, it emerged that when customers try to login to their accounts utilizing the “Sign up with Fb” possibility, an HTTP POST request is shipped to auth.grammarly[.]com to authenticate them utilizing a secret code.
Because of this, whereas Grammarly isn’t inclined to a token reuse assault like within the case of Vidio and Bukalapak, it’s nonetheless weak to a distinct sort of downside whereby the POST request could be altered to substitute the key code with an entry token obtained from the aforementioned malicious web site to achieve entry to the account.
“And like with the opposite websites, the Grammarly implementation didn’t carry out token verification,” Carmel mentioned, including, “an account takeover would give an attacker entry to the sufferer’s saved paperwork.”