VMware warned prospects on Monday that proof-of-concept (PoC) exploit code is now obtainable for an authentication bypass flaw in vRealize Log Perception (now often known as VMware Aria Operations for Logs).
“Up to date VMSA to notice that VMware has confirmed that exploit code for CVE-2023-34051 has been revealed,” the corporate stated in an replace to the unique advisory.
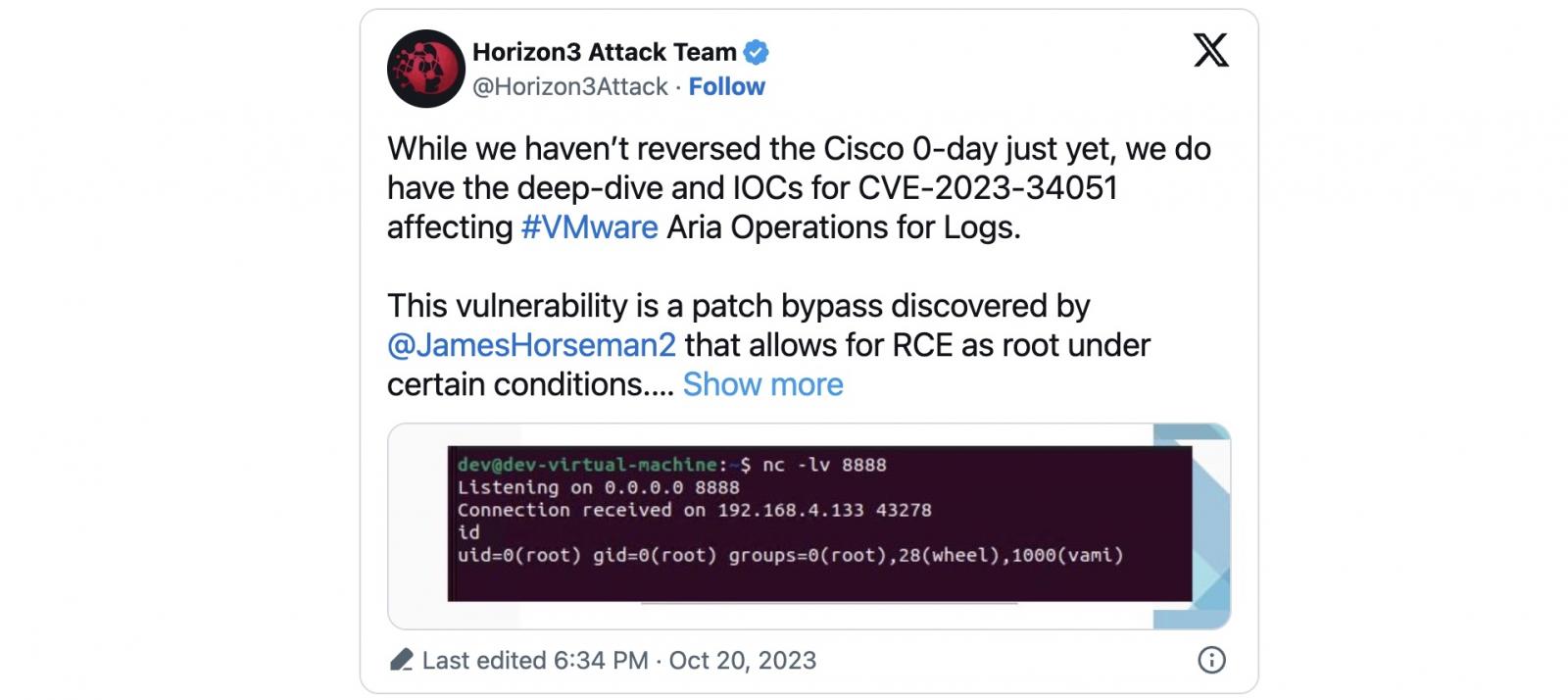
Tracked as CVE-2023-34051, it permits unauthenticated attackers to execute code remotely with root permissions if sure situations are met.
Profitable exploitation hinges on the attacker compromising a number throughout the focused setting and possessing permissions so as to add an additional interface or static IP deal with, in accordance with Horizon3 safety researchers who found the bug.
Horizon3 revealed a technical root trigger evaluation for this safety flaw on Friday with further info on how CVE-2023-34051 can be utilized to realize distant code execution as root on unpatched VMware home equipment.
The safety researchers additionally launched a PoC exploit and a listing of indicators of compromise (IOCs) that community defenders may use to detect exploitation makes an attempt inside their environments.
“This POC abuses IP deal with spoofing and varied Thrift RPC endpoints to attain an arbitrary file write,” the Horizon3 Assault Group stated.
“The default configuration of this vulnerability writes a cron job to create a reverse shell. You’ll want to change the payload file to fit your setting.
“For this assault to work, an attacker should have the identical IP deal with as a grasp /employee node.”
Bypass for a RCE exploit chain
This vulnerability can be a bypass for an exploit chain of important flaws patched by VMware in January, enabling attackers to realize distant code execution.
The primary (CVE-2022-31706) is a listing traversal bug, the second (CVE-2022-31704) is a damaged entry management flaw, whereas the third, an info disclosure bug (CVE-2022-31711), permits attackers to realize entry to delicate session and software data,
Attackers can chain these vulnerabilities (collectively tracked as VMSA-2023-0001 by VMware) to inject maliciously crafted recordsdata into the working system of VMware home equipment working unpatched Aria Operations for Logs software program.
When Horizon3 safety researchers launched a VMSA-2023-0001 PoC exploit one week after the corporate pushed safety updates, they defined that their RCE exploit “abuses the assorted Thrift RPC endpoints to attain an arbitrary file write.”
“This vulnerability is simple to use nonetheless, it requires the attacker to have some infrastructure setup to serve malicious payloads,” they stated.
“Moreover, since this product is unlikely to be uncovered to the web, the attacker probably has already established a foothold some other place on the community.
Nonetheless, menace actors steadily exploit vulnerabilities inside beforehand compromised networks for lateral motion, making weak VMware home equipment helpful inside targets.
In June, VMware warned prospects about one other important distant code execution vulnerability in VMware Aria Operations for Networks (tracked as CVE-2023-20887) being exploited in assaults.