The variety of Cisco IOS XE units hacked with a malicious backdoor implant has mysteriously plummeted from over 50,000 impacted units to only some hundred, with researchers not sure what’s inflicting the sharp decline.
This week, Cisco warned that hackers exploited two zero-day vulnerabilities, CVE-2023-20198 and CVE-2023-20273, to hack over 50,000 Cisco IOS XE units to create privileged consumer accounts and set up a malicious LUA backdoor implant.
This LUA implant permits the menace actors to remotely execute instructions at privilege degree 15, the very best privilege degree on the gadget.
Nonetheless, this implant doesn’t embody persistence, that means a reboot will take away the backdoor. Nonetheless, any native customers created in the course of the assault will stay.
For the reason that launch of this information, cybersecurity corporations and researchers have discovered roughly 60,000 out of the 80,000 publicly uncovered Cisco ISO XE units to be breached with this implant.
Mysterious drop in detected Cisco implants
On Saturday, a number of cybersecurity organizations reported that the variety of Cisco IOS XE units with a malicious implant has mysteriously dropped from roughly 60,000 units to solely 100-1,200, relying on the totally different scans.
Onyphe Founder & CTO Patrice Auffret advised BleepingComputer that he believes the menace actors behind the assaults are deploying an replace to cover their presence, thus inflicting the implants to be not seen in scans.
“For the second day in a row, we see the variety of implants have drastically dropped in a short while (see screenshots hooked up). Principally, they seem to have been virtually all rebooted (because the identified implant would not survive a reboot) or have been up to date.”
“We consider it’s the motion from the unique menace actor which is making an attempt to repair a problem that ought to not have been there from the start. The truth that the implant was really easy to detect remotely was a mistake from their facet.
“They’re most likely deploying an replace to cover their presence.”
Piotr Kijewski, the CEO of The Shadowserver Basis, additionally advised BleepingComputer that they’ve seen a pointy drop in implants since 10/21, with their scans solely seeing 107 units with the malicious implant.
“The implant seems to have been both eliminated or up to date indirectly,” Kijewski advised BleepingComputer by way of e-mail.
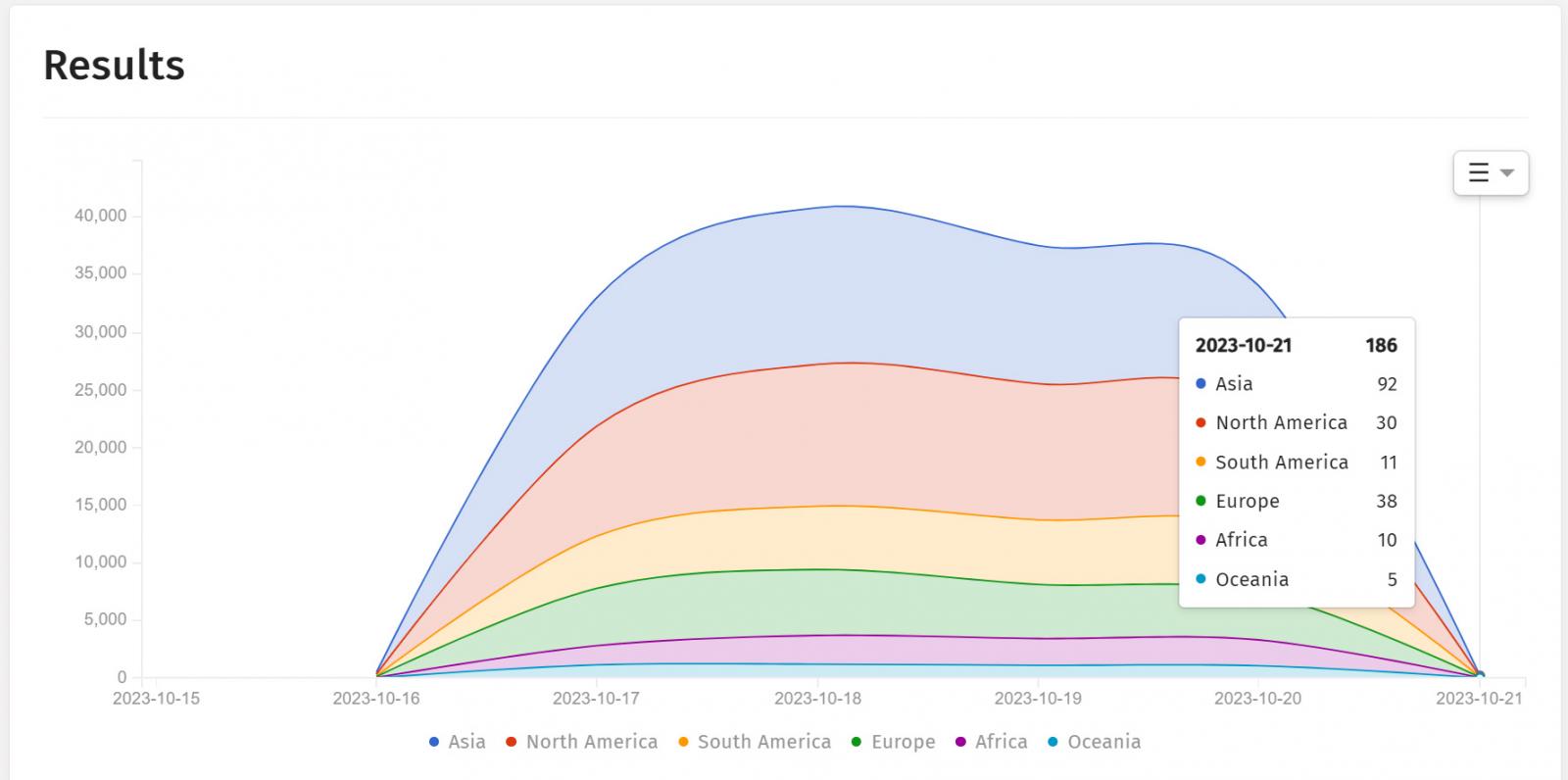
Supply: ShadowServer
One other concept is {that a} grey-hat hacker is automating the reboot of impacted Cisco IOS XE units to clear the implant. A comparable marketing campaign was seen in 2018 when a hacker claimed to have patched 100,000 MikroTik routers so they might not be abused for cryptojacking and DDoS campaigns.
Nonetheless, Orange Cyberdefense CERT for the Orange Group advised BleepingComputer that they don’t consider {that a} grey-hat hacker is behind the lower in implants however fairly that this could possibly be a brand new exploitation part.
“Please observe {that a} potential hint cleansing step is underway to cover the implant (following exploitation of #CVE-2023-20198),” tweeted Orange Cyberdefense CERT.
“Even when you’ve got disabled your WebUI, we suggest that you just perform an investigation to ensure that no malicious customers has been added and that its configuration has not been altered.”
One other chance shared by safety researcher Daniel Card is that the numerous units breached with implants had been merely a decoy to cover the actual targets in assaults.
Sadly, all we now have are theories at the moment. Till Cisco or different researchers can look at a beforehand breached Cisco IOS XE gadget to see in the event that they had been merely rebooted or if new modifications had been made, there is no such thing as a method to know what occurred.
BleepingComputer has contacted Cisco with questions concerning the drop in implants however has not obtained a reply at the moment.