The time between a vulnerability being found and hackers exploiting it’s narrower than ever – simply 12 days. So it is smart that organizations are beginning to acknowledge the significance of not leaving lengthy gaps between their scans, and the time period “steady vulnerability scanning” is rising in popularity.
Hackers will not wait on your subsequent scan
One-off scans could be a easy ‘one-and-done’ scan to show your safety posture to clients, auditors or buyers, however extra generally they discuss with periodic scans kicked off at semi-regular intervals – the trade customary has historically been quarterly.
These periodic scans offer you a point-in-time snapshot of your vulnerability standing – from SQL injections and XSS to misconfigurations and weak passwords. Nice for compliance in the event that they solely ask for a quarterly vulnerability scan, however not so good for ongoing oversight of your safety posture, or a sturdy assault floor administration program. With a contemporary CVE created each 20 minutes, you run the danger of getting an outdated view of your safety at any given second.
It is extremely seemingly that a number of the 25,000 CVE vulnerabilities disclosed final yr alone will have an effect on you and your enterprise within the gaps between one-off or semi-regular scans. Simply have a look at how usually you must replace the software program in your laptop computer… It will probably take weeks and even months earlier than vulnerabilities are patched too, by which period it might be too late. With the potential harm to your enterprise these vulnerabilities may trigger, there’s merely no substitute for steady scanning in 2023.
Steady vulnerability scanning gives 24/7 monitoring of your IT setting and automation to scale back the burden on IT groups. This implies points could be discovered and glued quicker, closing the door on hackers and potential breaches.
The sluggish tempo of compliance
Let’s be trustworthy, a variety of firms begin their cyber safety journey as a result of somebody tells them they need to, whether or not that is a buyer or trade compliance framework. And a variety of the necessities on this house can take time to evolve, nonetheless citing issues like an “annual penetration take a look at” or “quarterly vulnerability scan”. These are legacy ideas from years in the past when attackers had been few on the bottom, and this stuff had been seen as ‘good to have.’
Consequently, many organizations nonetheless deal with vulnerability scanning as a nice-to-have or a compliance field to tick. However there’s a world of distinction between semi-regular scanning and correct, steady vulnerability testing and administration – and understanding that distinction is essential for enhancing safety somewhat than simply spending cash on it.
The easy reality is that new vulnerabilities are disclosed daily, so there’s all the time the potential for a breach, much more so should you’re usually updating cloud companies, APIs, and functions. One small change or new vulnerability launch is all it takes to depart your self uncovered. It is now not about ticking packing containers – steady protection is now a ‘will need to have,’ and organizations who’re extra mature of their cyber safety journey understand it.
Steady assault floor monitoring
It isn’t simply new vulnerabilities which might be essential to observe. Daily, your assault floor modifications as you add or take away gadgets out of your community, expose new companies to the web, or replace your functions or APIs. As this assault floor modifications, new vulnerabilities could be uncovered.
To catch new vulnerabilities earlier than they’re exploited, that you must know what’s uncovered and the place – on a regular basis. Many legacy instruments do not present the appropriate stage of element or enterprise context to prioritize vulnerabilities; they deal with all assault vectors (exterior, inside, cloud) the identical. Efficient steady assault floor monitoring ought to present the enterprise context and canopy all assault vectors – together with cloud integrations and community modifications – to be actually efficient.
Assault floor administration is now not only a technical consideration both. Boards are more and more recognizing its significance as a part of a sturdy cyber safety program to safeguard operations, whereas it is a key requirement for a lot of cyber insurance coverage premiums.
How a lot is an excessive amount of?
Steady scanning doesn’t suggest fixed scanning, which may produce a barrage of alerts, triggers and false positives which might be practically not possible to maintain on high off. This alert fatigue can decelerate your methods and functions, and tie your group up in knots prioritizing points and removing false positives.
Intruder is a contemporary safety software that cleverly will get spherical this downside by kicking off a vulnerability scan when a community change is detected or a brand new exterior IP tackle or hostname is spun up in your cloud accounts. This implies your vulnerability scans will not overload your group or your methods however will decrease the window of alternative for hackers.
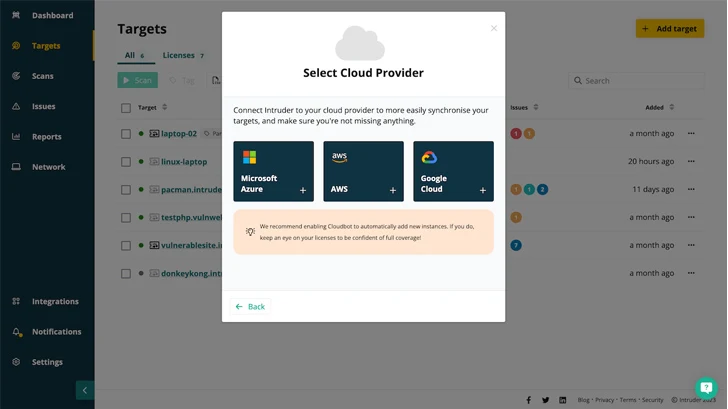 |
| Trendy safety instruments like Intruder combine along with your cloud suppliers, so it’s simple to see which methods are stay and to run safety checks when something modifications. |
How usually do that you must scan for compliance?
This is determined by which compliance you are searching for! Whereas SOC 2 and ISO 27001 offer you some wiggle room, HIPAA, PCI DSS and GDPR explicitly state scanning frequency, from quarterly to every year. However utilizing these requirements to find out the appropriate time and frequency for vulnerability scanning won’t be proper for your enterprise. And doing so will improve your publicity to safety dangers because of the quickly altering safety panorama.
If you wish to truly safe your digital belongings and never simply tick a field for compliance, that you must go above and past the necessities stipulated in these requirements – a few of that are out of step with in the present day’s safety wants. Right now’s agile SaaS companies, on-line retailers that course of excessive quantity transactions or take card funds, and anybody working in highly-regulated industries like healthcare and monetary companies, want steady scanning to make sure they’re correctly protected.
More durable, higher, quicker, stronger
Conventional vulnerability administration is damaged. With expertise in fixed flux as you spin up new cloud accounts, make community modifications or deploy new applied sciences, one-off scans are now not sufficient to maintain up with the tempo with the change.
With regards to closing the cyber safety gaps between scans that attackers look to take advantage of, sooner is healthier than later, however steady is finest. Steady scanning reduces the time to search out and repair vulnerabilities, delivers wealthy risk information and remediation recommendation, and minimizes your danger by prioritizing threats in line with the context of your enterprise wants.
About Intruder
Intruder is a cyber safety firm that helps organizations scale back their assault floor by offering steady vulnerability scanning and penetration testing companies. Intruder’s highly effective scanner is designed to promptly establish high-impact flaws, modifications within the assault floor, and quickly scan the infrastructure for rising threats. Operating hundreds of checks, which embody figuring out misconfigurations, lacking patches, and net layer points, Intruder makes enterprise-grade vulnerability scanning simple and accessible to everybody. Intruder’s high-quality stories are excellent to move on to potential clients or adjust to safety rules, equivalent to ISO 27001 and SOC 2.
Intruder provides a 14-day free trial of its vulnerability evaluation platform. Go to their web site in the present day to take it for a spin!