
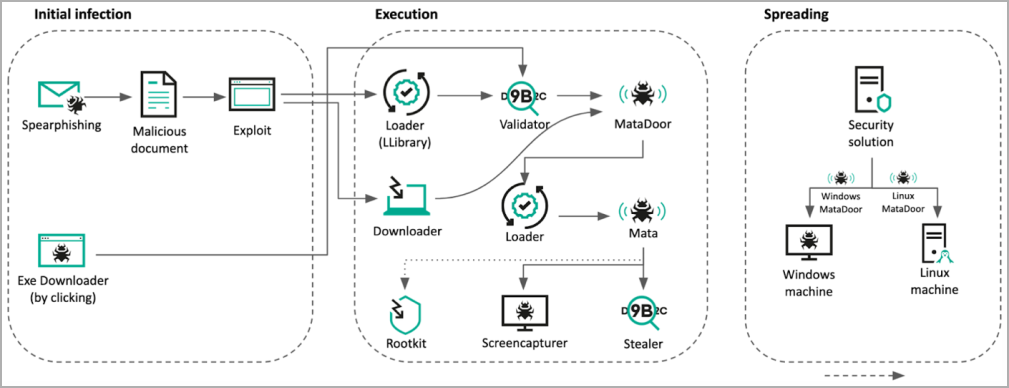
An up to date model of the MATA backdoor framework was noticed in assaults between August 2022 and Might 2023, focusing on oil and fuel corporations and the protection business in Jap Europe.
The assaults employed spear-phishing emails to trick targets into downloading malicious executables that exploit CVE-2021-26411 in Web Explorer to provoke the an infection chain.
The up to date MATA framework combines a loader, a primary trojan, and an infostealer to backdoor and achieve persistence in focused networks.
The MATA model in these assaults is just like earlier variations linked to the North Korean Lazarus hacking group however with up to date capabilities.
Notably, spreading malware throughout all reachable corners of the company community happens by breaching safety compliance options and exploiting their flaws.
Abusing EDR in assaults
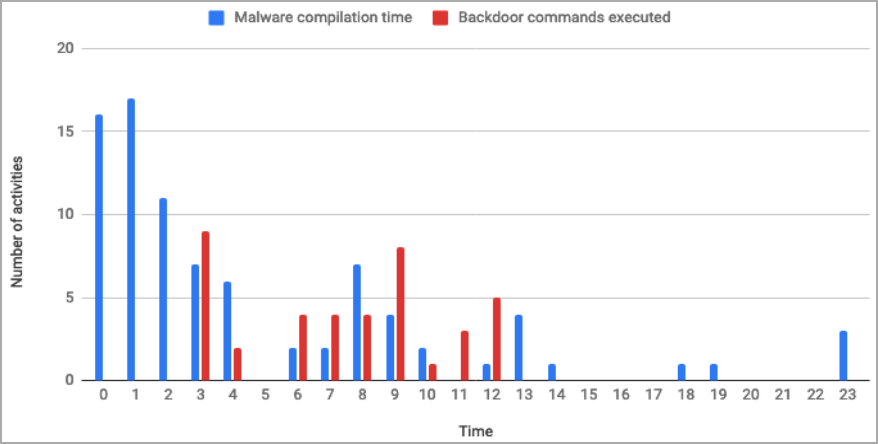
The cybersecurity firm found the exercise in September 2022 after inspecting two MATA samples speaking with command and management servers (C2) inside breached group networks.
Additional evaluation revealed that the breached methods had been monetary software program servers related to quite a few subsidiaries of the goal group.
The investigation revealed that the hackers had expanded their foothold from a single area controller on a manufacturing plant to all the company community.
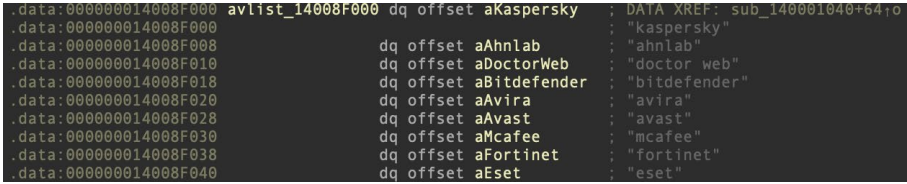
The assault continued with the hackers accessing two safety answer admin panels, one for endpoint safety and one for compliance checks.
The hackers abused the entry to the safety software program admin panel to carry out surveillance on the group’s infrastructure and to disseminate malware to its subsidiaries.
Up to date MATA malware
In relevant circumstances the place the targets had been Linux servers, the attackers employed a Linux variant of MATA within the type of an ELF file, which seems to be related in performance to the third era of the Home windows implant.
Kaspersky says it sampled three new variations of the MATA malware: one (v3) developed from the second era seen in previous assaults, a second (v4) dubbed ‘MataDoor,’ and a 3rd (v5) that was written from scratch.
The newest model of MATA is available in DLL type and options intensive distant management capabilities, helps multi-protocol (TCP, SSL, PSSL, PDTLS) connections to the management servers, and helps proxy (SOCKS4, SOCKS5, HTTP+net, HTTP+NTLM) server chains.
The 23 instructions supported by MATA fifth era embody actions to arrange connectivity, carry out administration of the implant, and retrieve data.
Crucial instructions supported by vanilla MATA are the next:
- 0x003: Connects to the C2 server utilizing a particular command set.
- 0x001: Initiates a brand new shopper session that manages varied instructions from Buffer-box.
- 0x006: Schedules a reconnect with particular delays and queued instructions.
- 0x007: Returns detailed system and malware data, encryption keys, plugin paths, and so on.
- 0x00d: Configures important settings like VictimID and connection parameters.
- 0x020: Initiates connection to C2 server and forwards site visitors.
- 0x022: Probes lively connection to given C2 servers and proxy checklist.
Extra plugins loaded onto the malware enable it to launch one other 75 instructions associated to data gathering, course of administration, file administration, community reconnaissance, proxy performance, and distant shell execution.
Different attention-grabbing findings embody a brand new malware module that may leverage detachable storage media reminiscent of USB to contaminate air-gapped methods, varied stealers able to capturing credentials, cookies, screenshots, and clipboard contents, and EDR/safety bypass instruments.
The researchers report that the hackers bypassed the EDR and safety instruments utilizing a publicly obtainable exploit for CVE-2021-40449, dubbed ‘CallbackHell.’
Using this instrument, the attackers alter kernel reminiscence and goal particular callback routines, which render endpoint safety instruments ineffective.
If that bypass technique failed, they switched to beforehand documented Deliver Your Personal Weak Driver (BYOVD) strategies.
Attribution unclear
Though Kaspersky beforehand related MATA with the North Korean state-backed hacking group Lazarus, the cybersecurity agency has bother associating the lately noticed exercise with excessive confidence.
Though there are nonetheless obvious hyperlinks to Lazarus exercise, the newer MATA variants and strategies reminiscent of TTLV serialization, multilayered protocols, and handshake mechanisms resemble extra carefully these of ‘5 Eyes’ APT teams like Purple, Magenta, and Inexperienced Lambert.
Additionally, the deployment of a number of malware frameworks and MATA framework variations in a single assault may be very unusual, indicating a very well-resourced menace actor.
For extra technical data on MATA malware and the strategies used within the newest assaults, try Kaspersky’s full report right here.


