A brand new report from Netskope detailing the highest methods utilized by cybercriminals to assault organizations discovered that cloud apps are more and more being utilized by menace actors, representing 19% of all clicks on spearphishing hyperlinks. The report additionally make clear the attackers’ targets based on their monetary or geopolitical motivations.
This Cloud and Risk report from Netskope, which is a U.S.-based firm specializing in Safe Entry Service Edge, mirrored the primary three quarters of 2023.
Soar to:
Prime methods utilized by cyberattackers
The most typical techniques and methods deployed by attackers to compromise methods, execute malicious code and talk with the contaminated system are cut up into 4 classes by Netskope: preliminary entry, malicious payloads execution, command and management and exfiltration.
Preliminary entry
The best manner for an attacker to entry a focused system is by way of its customers; that is very true if the focused group has patched all methods speaking with the web and is due to this fact not topic to frequent vulnerabilities exploitation. Social engineering is the most well-liked technique utilized by attackers to focus on organizations, whether or not it’s by e mail (spearphishing), voice (vishing), SMS (smishing) or by way of social networks.
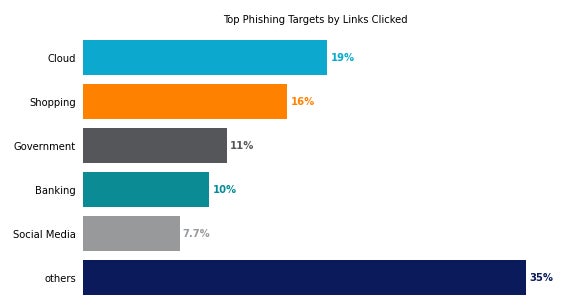
Netskope analyzed the phishing hyperlinks customers clicked on and concluded that customers most continuously clicked on phishing hyperlinks associated to cloud apps (19%), adopted by e-commerce web sites (16%) reminiscent of Amazon, eBay or much less well-liked purchasing websites (Determine A).
Determine A
In response to Netskope, one third of the phishing operations focusing on cloud apps centered on Microsoft merchandise. Netskope not too long ago reported that Microsoft OneDrive is the most well-liked cloud app utilized in enterprises, so it’s not a shock that attackers leverage this goal rather a lot, alongside Microsoft Groups, SharePoint and Outlook (Determine B).
Determine B

The second and third most-targeted apps are from Adobe (11%) and Google (8.8%).
Attackers nonetheless generally use emails to focus on customers, but the success price of these spearphishing operations is low. For starters, organizations usually make use of superior anti-phishing filters to intercept phishing emails earlier than they attain the customers. Secondly, organizations attempt to elevate consciousness about these assault campaigns and educate their customers to identify spearphishing emails. In response to those defenses, attackers deploy varied different methods to achieve their targets.
- Search Engine Optimization: Oftentimes, attackers create net pages constructed round particular units of key phrases that aren’t frequent on the web, to allow them to simply deploy website positioning methods to make sure their web page is available in first in search engines like google’ outcomes.
- Social media platforms and messaging apps: Attackers leverage well-liked social media platforms (e.g., Fb) or messaging apps (e.g., WhatsApp) to achieve targets with varied baits.
- Voicemail and textual content messages: Attackers goal customers with voicemail (vishing) or SMS (smishing) to unfold phishing hyperlinks. This technique has the advantage of focusing on cell phones, which are sometimes much less protected than computer systems.
- Private e mail packing containers: Attackers goal customers’ private e mail accounts, which are sometimes used on the identical methods the victims use for work and may result in delicate data entry.
With regards to utilizing hooked up recordsdata for phishing, 90% of the assaults use PDF recordsdata as a result of it’s a frequent format utilized in enterprises. Ray Canzanese, director of Netskope Risk Labs, informed TechRepublic by way of e mail, that, “PDFs are well-liked amongst attackers as a result of they’re so generally used for invoices, payments and different necessary correspondence. Adversaries create faux invoices and ship them to their victims. Typically, the one indicators that it’s malicious are the URL or telephone quantity it accommodates, and adversaries use obfuscation methods to cover that from safety options. These PDFs are created at such excessive quantity and with so many variants that it’s at present troublesome for some safety options to maintain up. As with every adversary traits, safety options will catch up and attackers will pivot to a brand new set of phishing methods.”
Malicious payloads execution
Malicious payloads will be executed by unsuspecting customers with the impact of offering the attacker with distant entry to methods throughout the group to function extra malicious actions, reminiscent of deploying ransomware or stealing data.
Attackers now use cloud storage apps a bit extra (55%) than net storage (45%) on common for the primary quarters of 2023 (Determine C).
Determine C
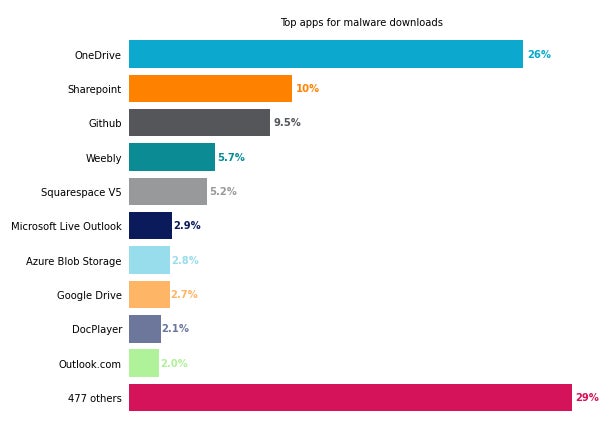
Microsoft OneDrive represents greater than 1 / 4 of the general utilization of cloud storage apps to host malware (26%), forward of SharePoint (10%) and GitHub (9.5%).
Malware communications and information exfiltration
Attackers principally use the HTTP (67%) and HTTPS (52%) protocols for communications between their malicious payloads and their command and management servers; these two protocols are typically absolutely allowed for customers, as they’re the primary vector for looking the web and will not be filtered by firewalls.
Far behind HTTP and HTTPS, the Area Title System protocol is utilized in 5.5% of malware communications. The DNS protocol, which is rarely blocked and filtered in organizations, just isn’t as stealthy as HTTP and HTTPS when transmitting information. Additionally, DNS makes it more durable for attackers to mix with authentic site visitors from the group and might transmit much less information at a time than HTTP or HTTPS.
Most prevalent menace actors and their motivations
WizardSpider is essentially the most prevalent menace actor
Probably the most prevalent menace actor as noticed by Netskope is Wizard Spider, who additionally goes by the aliases of UNC1878, TEMP.MixMaster or Grim Spider. Wizard Spider is chargeable for the TrickBot malware, which initially was a banking trojan however developed to a fancy malware that additionally deployed further third-parties’ malware reminiscent of ransomware.
Concerning potential affiliation, Canzanese informed TechRepublic that “practically each main cybercrime group right now makes use of an affiliate mannequin the place anybody can develop into an affiliate and use the group’s instruments towards targets of their selecting. Wizard Spider is not any totally different, with associates utilizing their TrickBot malware and a number of ransomware households.”
Risk actors’ major motivations and targets
In response to Netskope’s report, most menace actors motivated by monetary achieve originate from Russia and Ukraine; these menace actors have principally unfold ransomware moderately than every other type of malware.
On the geopolitical facet, Netskope noticed that the largest threats come from China, led by menuPass (also referred to as APT10, Stone Panda or Crimson Apollo) and Aquatic Panda.
Probably the most focused industries fluctuate between financially-motivated actors and geopolitical ones, with monetary companies and healthcare being essentially the most focused by geopolitical actors.
Australia and North America are the 2 most-targeted areas for monetary crime as in comparison with geopolitical focusing on. Once we requested Canzanese why Australia and North America have been focused, he replied, “If requested a distinct manner, the reply maybe turns into extra readily obvious: Why is the relative share of geopolitical adversary group exercise increased in the remainder of the world? Such exercise mirrors broader political, financial, navy or social conflicts. So the upper share of geopolitical adversary exercise in the remainder of the world seems to be the results of lively conflicts and the broader geopolitical local weather in these areas.”
How one can mitigate these cloud safety threats
Corporations ought to take these steps to mitigate such cloud safety threats:
- Deploy e mail safety options that may analyze hooked up recordsdata and hyperlinks to detect phishing and malware.
- Educate customers on easy methods to detect phishing and social engineering schemes that may put them or the corporate in danger. Specifically, customers mustn’t obtain any content material from the web, even when saved on cloud apps, that doesn’t originate from a trusted contact.
- Maintain all software program and working methods updated and patched with the intention to keep away from being compromised by a typical vulnerability.
Disclosure: I work for Development Micro, however the views expressed on this article are mine.


