A brand new Google Search malvertizing marketing campaign targets customers trying to obtain the favored Notepad++ textual content editor, using superior strategies to evade detection and evaluation.
Risk actors have been more and more abusing Google Adverts in malvertising campaigns to advertise pretend software program web sites that distribute malware.
In keeping with Malwarebytes, which noticed the Notepad++ malvertising marketing campaign, it has been reside for a number of months however managed to fly underneath the radar all this time.
The ultimate payload delivered to victims is unknown, however Malwarebytes says it is more than likely Cobalt Strike, which normally precedes extremely damaging ransomware deployments.
Abusing Google advertisements
The Notepad++ malvertizing marketing campaign promotes URLs which might be clearly unrelated to the software program venture but use deceptive titles displayed in Google Search consequence ads.
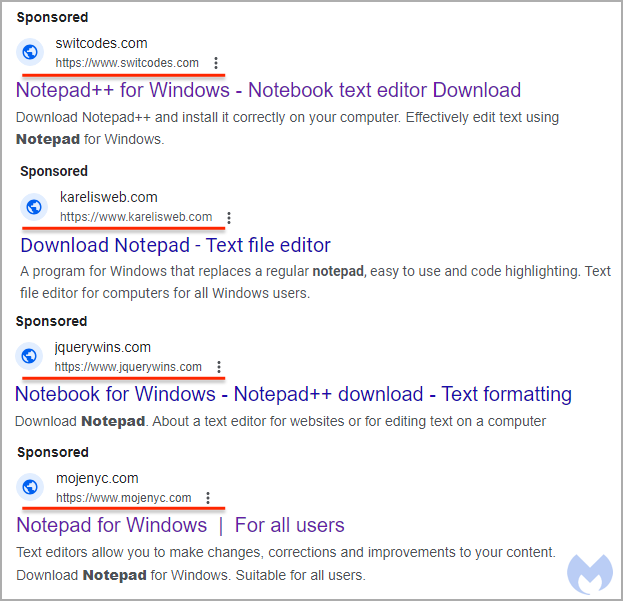
Supply: Malwarebytes
This search engine optimization technique is closely abused on this case, and since titles are far bigger and extra seen than URLs, many individuals are more likely to fall for the lure.
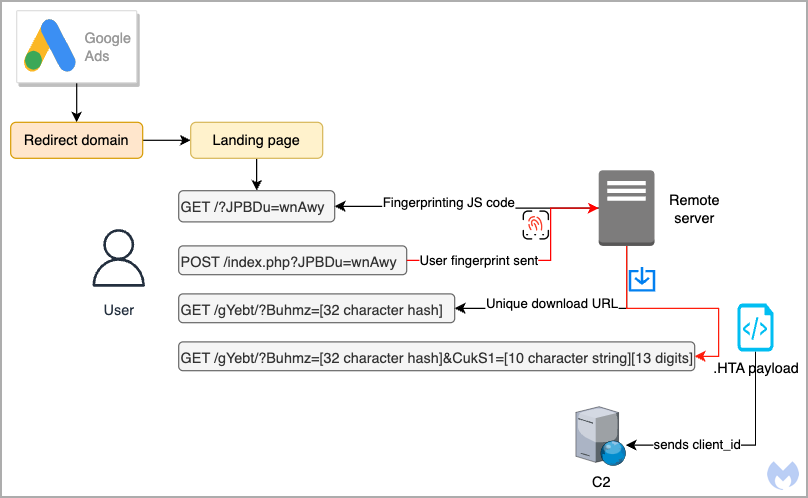
As soon as victims click on on any of the advertisements, a redirection step checks their IP to filter out customers more likely to be crawlers, VPNs, bots, and so on., main them to a decoy website that doesn’t drop something malicious.
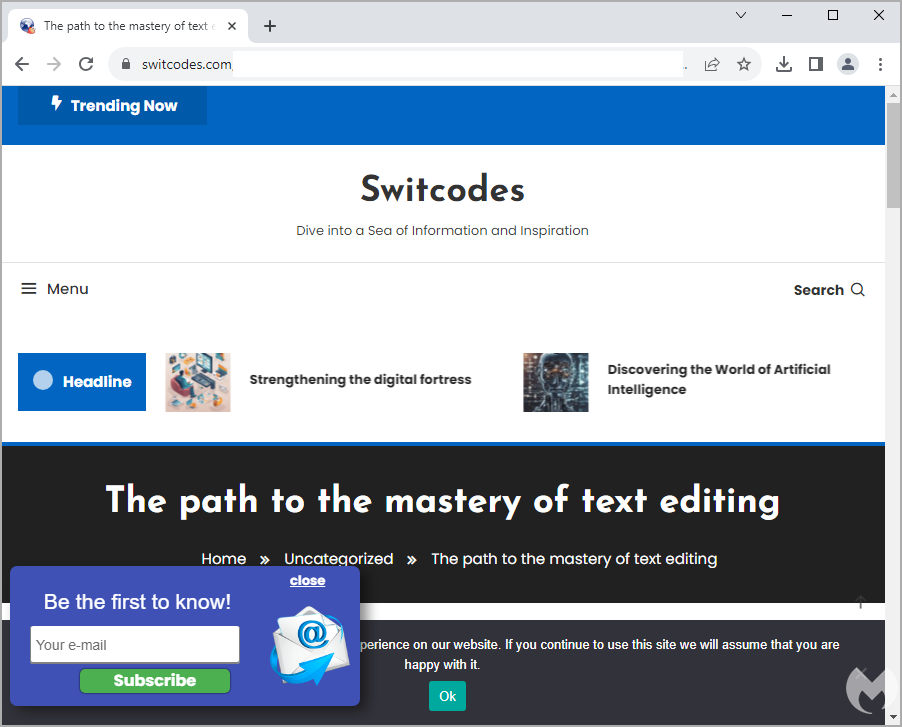
Supply: Malwarebytes
In distinction, professional targets are redirected to “notepadxtreme[.]com” which mimics the true Notepad++ website, that includes obtain hyperlinks for varied variations of the textual content editor.
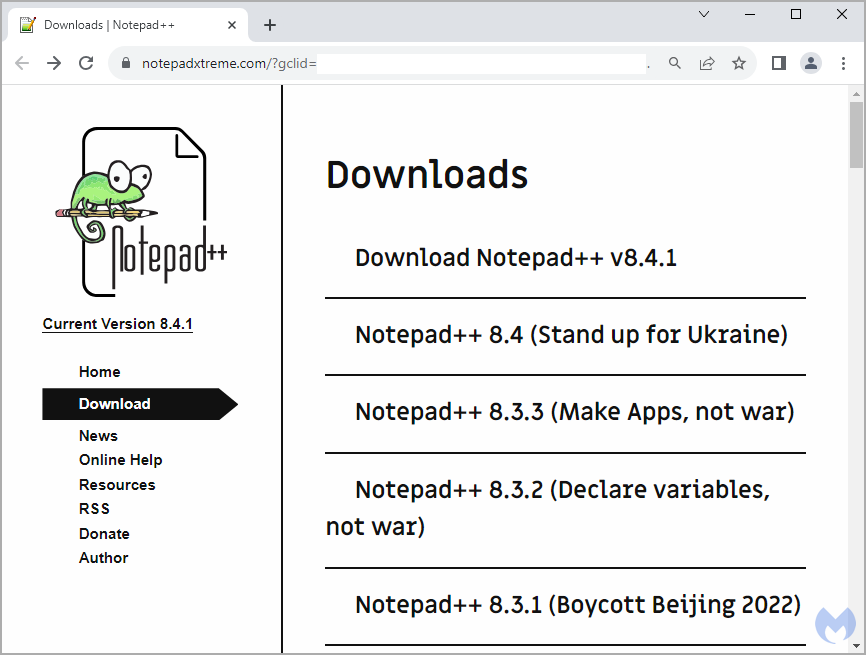
Supply: Malwarebytes
When guests click on on these hyperlinks, a second system fingerprint examine is carried out by a JavaScript snippet to validate that there aren’t any anomalies or indications that the customer is utilizing a sandbox.
Victims who’re marked as appropriate targets are then served an HTA script, which is assigned a novel ID, more likely to allow the attackers to trace their infections. That payload is served solely as soon as per sufferer, so a second go to leads to a 404 error.
Malwarebytes’ examination of the HTA did not produce any helpful data as a result of it not being weaponized on the time, however the analysts discovered the identical file in a VirusTotal add from July.
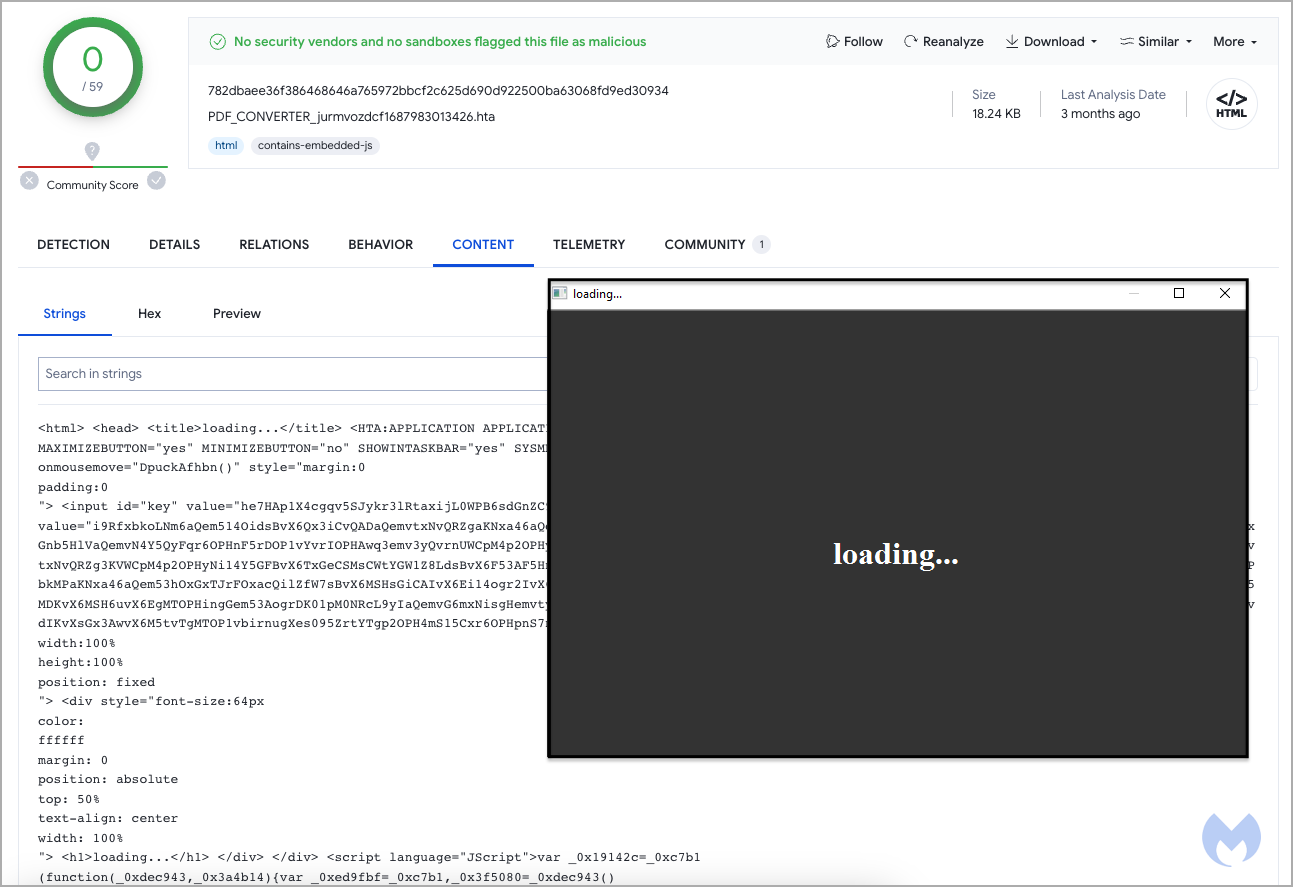
Supply: Malwarebytes
That file tried to connect with a distant area on a customized port, with the researchers believing it was possible a part of a Cobalt Strike deployment.
Supply: Malwarebytes
To keep away from downloading malware when on the lookout for particular software program instruments, skip promoted outcomes on Google Search and double-check that you’ve got landed on the official area.
If not sure in regards to the venture’s actual web site, examine its “About” web page, documentation, Wikipedia web page, and official social media channels.


